Elliptic curve cryptography encryption is a modern public key cryptographic system that is widely popular because it is more efficient, faster, and smaller compared to most cryptographic solutions. ECC is based on the elliptic curve theory that enables the creation of more efficient cryptographic keys. In addition, ECC’s asymmetric encryption has smaller key sizes making it lightweight.
Understanding ECC
Existing public encryption methods, including RSA and Diffie-Hellman, generate large numbers requiring high computational power. Therefore, they need vast resources to encrypt applications and may be unsuitable for use in resource-constrained mobile applications. The use of elliptic curves enables the creation of keys that are more efficient and faster. With ECC, the elliptic curve equation features generate mathematically robust and complex keys that provide a higher level of security. In addition, elliptical curve cryptography uses shorter key lengths that provide robust protection and are thus effective for securing mobile applications.
Applications of ECC
ECC encryption is one of the widely used application methods for digital signatures for popular cryptocurrencies like bitcoin. The cryptocurrencies utilize the Elliptic Curve Digital Signature Algorithm (ECDSA) key for cryptography purposes and signing transactions. Elliptic curve cryptography is applied in digital signatures using ECDSA key during key pair and key exchange. Also, different parts of SSL standards use ECDSA signing SSL certificates because of the low resources used. Other applications of ECC include:
- Proving ownership of cryptocurrencies like bitcoins
- Securing internal interactions and confidential data of the US government
- Maintaining and preserving anonymity for users using the TOR project
- Providing encryption signatures in Apple’s iMessage communication service
- Enable secure web browsing
Is ECC Different from Other Public Key Encryption Methods?
Organizations use ECC cryptographic algorithms for similar reasons as to why they would use RSA algorithms. For example, both RSA and ECC generate a private key and a public key infrastructure to enable two users or devices to communicate securely by exchanging a shared secret. However, the ECC public key encryption techniques have some benefits over RSA and other encryption methods. For example, a 256-bit ECC key provides almost an equivalent security level as a 3072-bit RSA key. Also, the elliptic curve cryptography algorithm permits systems with constrained resources, such as computational power, to utilize approximately 10% of the bandwidth and storage space that RSA algorithms would require.
Since ECC is based on the elliptic curve theory, it uses the properties of the elliptic curve equation to generate encryption keys. The approach contrasts with the traditional method of generation, where public-key cryptography algorithms generate large prime numbers. Other public-key cryptographic methods, such as Diffie-Hellman and RSA, can be used with the ECC encryption technique. Research shows that ECC cryptographic systems provide a level of encryption and protection using a 164-bit key, while other systems would require a 1,024-bit key to offer the same level of security. Because ECC security systems use small keys to provide high protection with lower battery resource usage and computing power, it is a preferred method for protecting mobile applications.
ECC Trapdoor Function
The ECC trapdoor function is one of the primary reasons the elliptic curve key is more effective and different than the RSA cryptographic key. The trapdoor function is a mathematical algorithm used in the ECC encryption method. The algorithm involves the hops needed to get to a various set of points and works as follows:
- First, you start on an arbitrary point on an elliptic curve and use the dot function to locate a new point.
- When you start at A:
- A dot B =-C (connect points A and B with a line that intersects at -C).
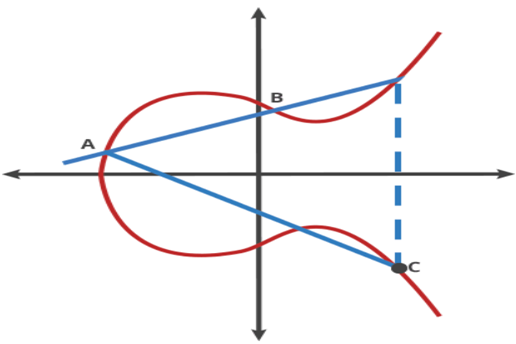
Source Ars Technica
- Reflect from –C to C across the X-axis and A dot C = -D (connect A and C with a line that intersects at -D).
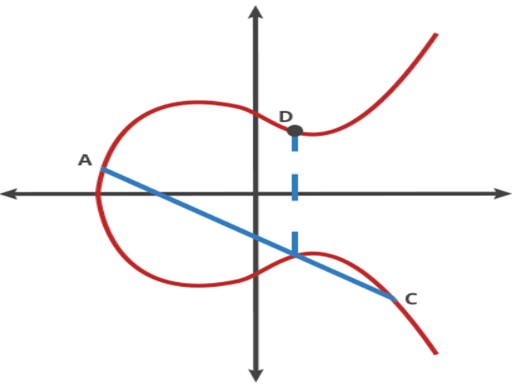
Source Ars Technica
- Reflect from –D to D across the X-axis and A dot D = -E (connect A and D with a line that intersects at -E).
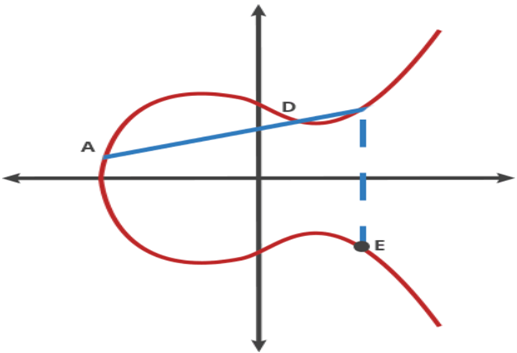
Source Ars Technica
- Reflect from –E to E across the X-axis.
This is a good trapdoor function because if a user knows the starting point (A) and the hops needed to reach the ending point E, it is simple to locate the ending point. However, if the user only knows the starting point and ending point, it is challenging to determine the number of hops needed. The same approach applies in ECC cryptography, where the public key cryptography is the starting EC point A to the ending EC point E, and the private key is the number of hops needed to get from A to E.
Advantages of Using ECC
ECC keys are smaller and more efficient compared to those of RSA and other public cryptographic methods. Thus, elliptic cryptography using public-key encryption is easier to process but challenging to reverse. In contrast, RSA encryption is based on the theory that a product of multiplication of large prime numbers is simple but factoring the product to go back to the original prime numbers is challenging.
In this regard, the usual 256-bit ECC key size is equivalent to a 3072-bit key length. The use of smaller, simpler, and more efficient ECC keys places ECC cryptography at an advantage. It is better than RSA cryptographic methods with the ability to consume fewer resources and less energy in small mobile devices.
Furthermore, ECC encryption is usually used together with Diffie-Hellman to enhance performance. ECC encryption does not perform RSA’s functions of communication and authentication, but it generates the ephemeral DH session key through the assistance of an elliptic curve private key. The associated SSL cipher suites contain the ECDHE-RSA encryption that complements DHE-based cipher suites.
The primary benefit of the elliptic curve cryptography used in conjunction with Diffie-Hellman (ECDHE-RSA) over using a plain Diffie-Hellman (DHE-RSA) is it has optimized performance, provides a similar level of protection but with lesser keys.
While there may be concerns regarding implementing ECC certificates, which include a source of random numbers for making signatures, the benefits of elliptic curve cryptography outweigh those of the traditional RSA algorithm. Besides, emerging technologies like quantum computing place traditional public encryption methods at risk of being compromised, leaving ECC encryption as a viable replacement option.


