The history of cybersecurity begins long before modern ransomware gangs, cloud breaches, and nation-state hacking dominated headlines. What started as a niche concern around access, experimentation, and early network misuse has grown into one of the defining operational and geopolitical issues of the digital age.
Today, cybersecurity shapes how governments defend infrastructure, how businesses manage risk, and how ordinary people protect their money, identity, and devices. Understanding how the field evolved helps explain why modern security programs look the way they do.
This article traces cybersecurity from its early academic roots to the commercial internet, criminal monetization, large-scale breaches, and the modern security industry.
From Academic to Criminality
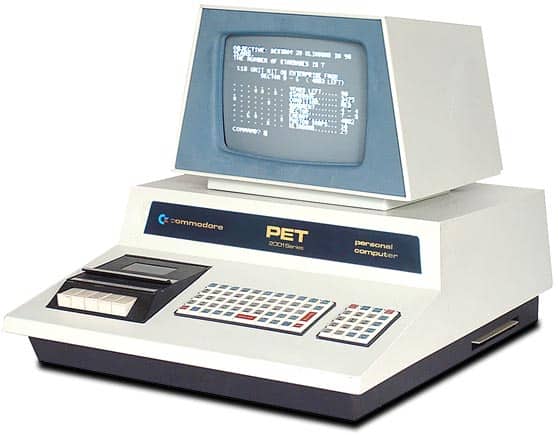
For most of the 1970s and 1980s, when computers and the internet were still under development, computer security threats were easily identifiable.
A majority of the threats were from malicious insiders who gained access to documents that they weren’t supposed to view. Therefore, computer security in software programs and the security involving risk and compliance governance evolved separately.
Network breaches and malware existed at this time. But they were used for purposes other than financial gain.
For instance, the Russians used them to deploy cyber power as a form of weapon. Similarly, Marcus Hoss, a German computer hacker, hacked into an internet gateway. Hoss used the gateway located in Berkeley to connect to the Arpanet. He then proceeded to access 400 military computers, including the Pentagon’s mainframes. Hoss’ primary intent was to acquire information to sell to the Russian spy agency, KGB. An astronomer, Clifford Stoll, however, used honeypot systems to detect the intrusion and foil the plot.
Notably, this attack was the start of severe computer crimes utilizing virus intrusion. Viruses were no longer used just for academic purposes.
In the 1970s, Robert Thomas, a researcher at BBN technologies, realized the possibilities of creating a program capable of moving in a network and leaving behind a trail. This discovery led to the invention of the first computer worm. The worm was called Creeper, and it was designed to travel in between Tenex terminals. It printed the message “I’M THE CREEPER: CATCH ME IF YOU CAN.”
As described below, the creation of viruses and worms, such as the Morris computer worm, had severe repercussions. They almost led to a complete wipeout of the early internet. Virus attacks subsequently spurred an immense growth of the antivirus industry.
The 1980s – The Era of Computer Worms
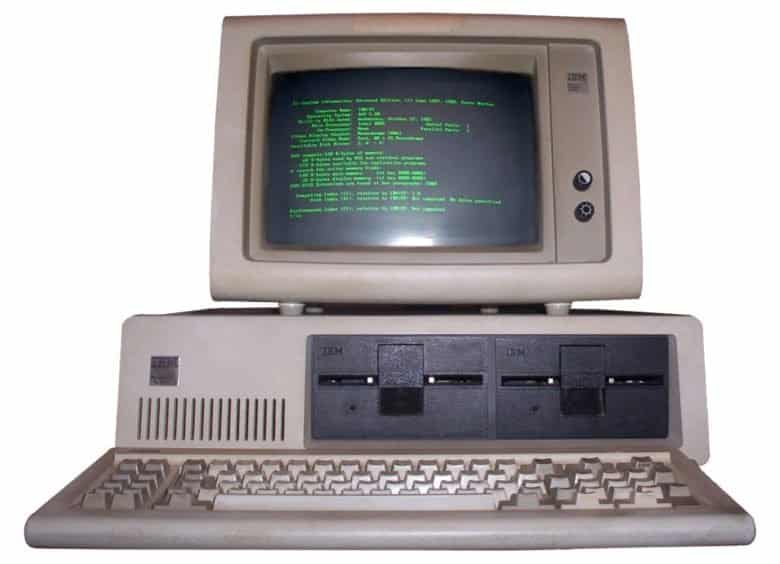
The creation of the first computer worm was a milestone in the history of cybersecurity. Researchers trace the very first disastrous computer worm to Robert T. Morris, who was a graduate student from Cornwell University. Morris was curious about the internet size created a worm in 1988 to gauge it. The worm was designed to infect UNIX systems such that it would count the total connections present on the web. Morris thus wrote a worm program that would propagate across a set of networks, use a known vulnerability to infiltrate UNIX terminals, and then replicate itself.
However, this turned out to be a huge mistake. A programming error caused the worm to infect machine after machine. As a result, networks clogged, causing the connected systems to crash. The worm replicated aggressively to a point where the internet slowed down to a crawl, leaving untold damage in its wake. This worm is the first to have received full media coverage and was among the very first programs written to exploit system vulnerabilities.
The worm’s effects lasted beyond the crashed internet and connected systems. For one, Morris became the first person to be charged successfully under the Computer Fraud and Abuse Act. He was fined $10000, sentenced to probation of three years, and dismissed from Cornwell (although he went on to become an MIT tenured professor). The act further led to the development of a Computer Emergency Response Team, the predecessor of US-CERT.
The Morris worm triggered the start of an entirely new field in computer security. It led to more people researching on how they can create deadlier and more effective worms and viruses. The more worms evolved, the greater their effect on networks and computer systems. Worms and viruses, in turn, led to the rise of antivirus solutions as a means of countering the worm and virus attacks.
The 1990s – The Rise of Computer Viruses
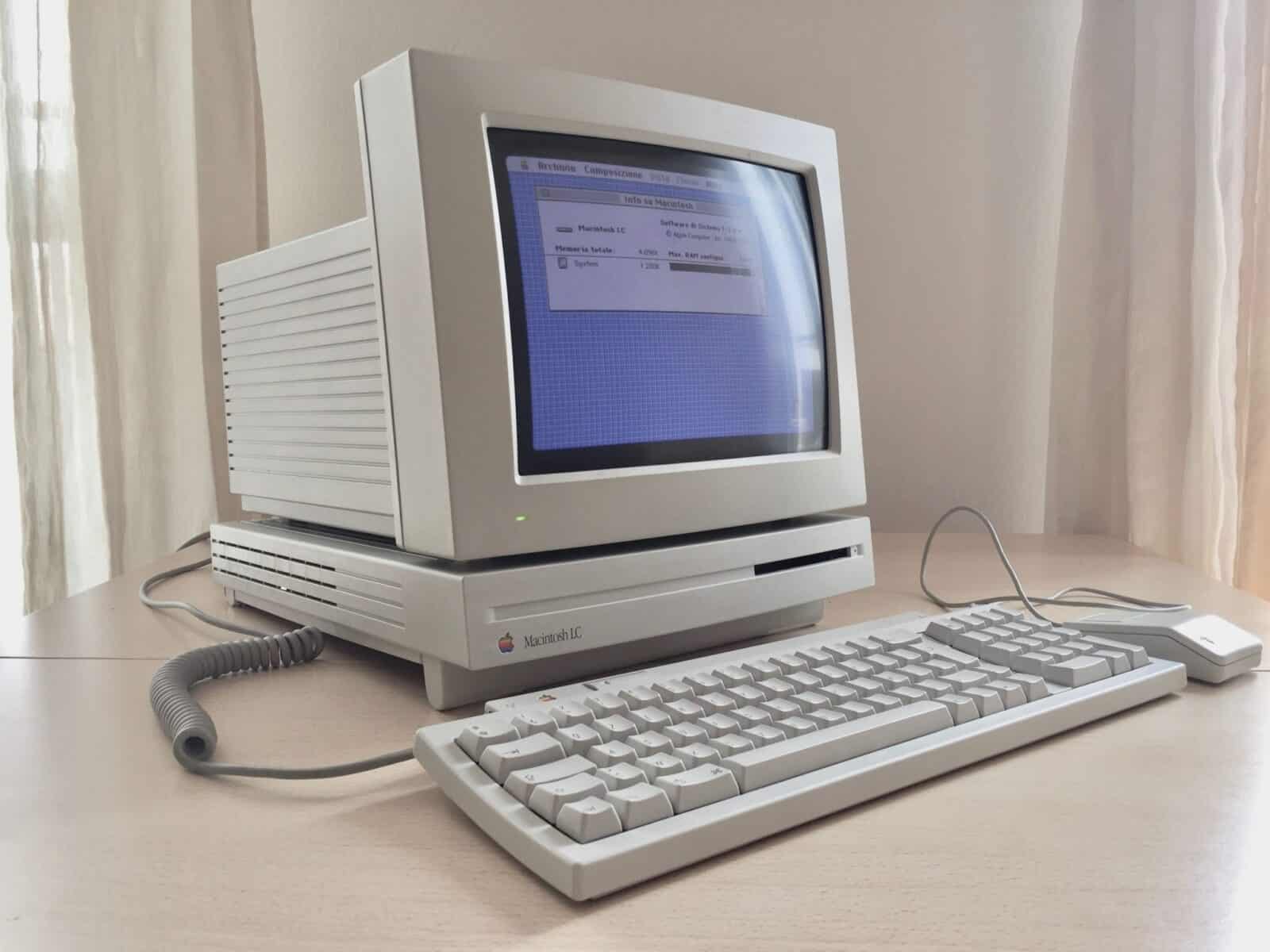
As previously mentioned, the Morris worm paved the way for newer types of malicious programs. Viruses were more aggressive programs that came into light in the 1990s. Viruses such as I LOVE YOU and Melissa infected tens of millions of computers, causing a worldwide failure of email systems. Most of the virus attacks were primarily concerned with financial gains or strategic objectives. However, inadequate security solutions at the time caused a huge number of unintended victims to be affected. The attacks became center-stage as they headlined in major news outlets in different parts of the world.
Suddenly, cyber threats and attacks were a huge concern necessitating the creations of an immediate solution. This problem gave birth to antivirus software solutions. The programs were designed to detect the presence of viruses and to prevent them from accomplishing their intended tasks. More so, the primary delivery method for viruses was the use of malicious email attachments. The virus attacks, most importantly, caused increased awareness, especially with regards to opening email messages originating from unknown people.
The Antivirus Industry
The early 1990s saw a sharp growth of companies creating and retailing antivirus products. The products were scanning computer systems for the presence of viruses or worms. At the time, the available antivirus solutions scanned business IT systems and tested them with signatures written in a database. Although the signatures were initially file computed hashes, they later incorporated strings similar to those present in malware.
However, two significant problems had high impacts on the effectiveness of these early antivirus solutions. The issues persist today in some of the current cybersecurity solutions. The problems included the intensive use of resources and a large number of false positives. The former caused the most problems for users since antivirus solutions scanning systems used a lot of the available resources such that they interrupted user activities and productivity.
During the same period, the malware samples produced every day increased in size and scope. Whereas only a few thousands of malware samples existed in the 1990s, the number had grown to at least 5 million by the year 2007. As a result, the legacy antivirus solutions could not handle such a capacity as security professionals were unable to write signatures that would keep up with the problems as they emerged. The challenge called for a newer approach that would offer adequate protection to all systems.
The endpoint protection platforms slowly proved to be better security solutions for countering an increasing rate of virus attacks and other related malware. Rather than depending on static signatures as the primary technique for detecting viruses, researchers used signatures to identify malware families. The solutions relied on the premise that malware samples were deviations from other existing samples. The endpoint protection platform approach was more effective. Customers realized that it was possible to detect and stop unknown malware since only a signature of other existing malware was required.
Secure Sockets Layer

In light of the increasing virus and worm attackers, security professionals required to identify means for protesting users when browsing through the internet. The secure sockets layer (SSL) came to be in 1995. SSL internet protocol enables users to access the web securely and perform activities such as online purchases. Netscape developed the SSL protocol shortly after National Center for Supercomputing Applications developed and released the first internet browser. Netscape released the secure protocol in 1995, and it became the core for developing languages such as HyperText Transfer Protocol Secure (HTTPS).
The rise of the first hacker group

There are many hacker groups and organized cybercrime groups today. They consist of individuals with a specific hacking skill and usually launch cyberattack campaigns characterized by different objectives. Anonymous was the first hacker group that came into the limelight on October 1, 2003. The group doesn’t have a particular leader, and the members are from different offline and online community users. It first made news when it hacked a website belonging to the Church of Scientology using distributed denial of service attacks (DDoS). To date, Anonymous has been linked to many high-profile attack incidents and has motivated other groups such as Lazarus and Apt38, to execute large-scale cyberattacks.
Credit card hacks in the 2000s

In the 2000s or the new millennium, as it popularly came to be known, cyberattacks started being more targeted. One of the most memorable attacks during this period includes the first reported case of serial data breaches targeting credit cards. These were perpetrated between 2005 and 2007 when Albert Gonzales created a cybercriminal ring for compromising credit card systems. The group executed attacks that successfully stole confidential information from at least 45.7 million cards[1]. These belonged to customers frequenting TJX retailers.
The breach caused the giant retailer a loss amounting to $256 million. More so, since it involved compromising regulated data, the breach caused the involvement of US authorities. The company was further required to set aside funds that would be used to compensate the affected victims. Gonzales received a sentence of 40 years in prison imprisonment. TJX was unprotected when the breach occurred and other organizations saw this as a cue for protecting themselves with sophisticated cybersecurity programs.
EternalBlue: Lateral movement attack techniques

Lateral movement attack techniques allow cybercriminals to run codes, issue commands, and to spread across a network. Such methods have been in play for several years and are hence not new to system administrators. Lateral movement vulnerabilities have been present in some operating system protocols for many years, enabling cybercriminals to execute lateral stealth attacks. EternalBlue constitutes of a notable example of lateral movement vulnerability.
The EternalBlue vulnerability allows an attacker to exploit SMB protocols used to share files across a network. As a result, the protocol highly attracts cyber adversaries. Shadow Brokers leaked the protocol on April 14, 2017, and the notorious Lazarus group used it as an exploit for the infamous WannaCry attack on May 12, 2017. The WannaCry attack was a global ransomware attack targeting health institutions mostly in Europe. The attack was quite devastating as it caused health services to halt for almost a week.
The EternalBlue exploit has also been used to execute other high-profile cyberattacks. On June 27, 2017, the vulnerability was exploited in the NotPeyta attacks which targeted banks, ministries, electricity, and newspaper firms across Ukraine. The attack spread in other countries, including France, the US, Russia, Poland, Italy, Australia, and the United Kingdom. It was also used to execute Retefe banking trojans.
Cybersecurity regulations and laws

The evolution of technology in different industries has propelled cyber laws to emerge. These laws intend to protect systems and confidential data. Some of the notable regulations in cybersecurity history include the Health Insurance Portability and Account Act (HIPAA). HIPAA became law on August 21, 1996, with the intent of improving employees’ accountabilities in regards to insurance coverages. The bill has nevertheless been amended over the years to focus more on protecting employee personally identifiable information (PII).
Also, the Gramm-Leach-Bliley Act (GLBA), also called the Financial Modernization Act, was enacted in 1999 to protect the personal data of customers of financial institutions. The law requires a financial organization to provide detailed information on the strategies it intends to use when securing a customer’s private data. To comply with the law, financial organizations must always alert customers on how they will share their personal information. More so, the law stipulates that customers have the right to deny financial organizations the rights to share sensitive data. Also, the financial institution must maintain a documented information security program for protecting customers’ sensitive data.
Notwithstanding, in 2003, the Federal Information Security Management Act (FISMA) was legislated to provide organizations with guidance for securing information systems. The law defines a complex framework to be applied in securing government IT assets, data, and operations from natural or manmade disasters. The act followed the enactment of the E-Government Act (Public Law 107-347), which outlined the main threats that affect information systems. The E-government Act also outlined the need for adopting effective security measures for securing against the threats. FISMA falls under the E-Government Act.
According to the FISMA act, all federal agencies must develop and document agency-wide programs for protecting information systems. For an agency to be FISMA compliant, it must observe the following guidelines:
- Conduct frequent inventories of current security measures
- Analyze existing or anticipated threats
- Design working security plans
- Designate security professionals for overs sing the implementation of the security plans and continuously monitor its effectiveness
- Document plans for reviewing the security plans and periodically assess its security operations
There are other recently enacted regulations. An example is the General Data Protection Regulation (GDPR). This regulation provides mandatory guidelines for institutions handling PII data and imposes hefty fines any incidence of non-compliance. The GDPR protects data specifically belonging to members of the European Union. The fundamental tenet of the regulation is ensuing organizations implement adequate data protection controls, which include encryption for both data in transit and data at rest.
Also, every organization has to seek the explicit consent of data owners before using their confidential information for any reason. Organizations stand to be fined at least 4% of their annual profits for failing to properly secure PII information or using customer data without their permission. They can also be fined 4% when a breach occurs due to inadequate security measures.
Cybersecurity frameworks

In addition to cybersecurity laws and regulations is the proposal of different frameworks. These frameworks intend to guide federal and private organizations to secure their information systems better. The US Department of Homeland Security strategy, for example, was rolled out in 2018. This strategy proposes guidelines that an organization can use to detect and identify risks. It further highlights the techniques for reducing cyber vulnerabilities, lowering the threat levels, mitigating the aftermath of a cyber-attack, etc.
The Federal Cybersecurity Research and Development (R&D), on the other hand, has been active since 2012 and is updated every four years. This framework incorporates the idea that it is near impossible to be 100% protected from cyber-attacks. As a result, the framework guides federal agencies on effective risk detection and response. It provides guidelines for analyzing risk history and classifying them based on the levels of severity. Organizations tend to use both frameworks to implement and accordingly update strong cybersecurity programs.
Recent cybersecurity attacks
Today, cybercrime has become mainstream. Cybercriminals have been using attacks for various monetary gains. Cybercrime evolved since the 80s and 90s when worm and malware attacks intended to allow unauthorized access.
The following sections provide some facts regarding recent cyberattacks. It is followed by what the attacks mean for the future of cybersecurity.
Yahoo attacks: Yahoo was the victim of one of the worst attacks in 2013 and 2014. The attacks resulted in a compromise of Yahoo accounts belonging to over 3 billion users[2]. The attacks exploited unpatched vulnerabilities. Hackers used spear-phishing techniques to install malware on Yahoo’s servers, allowing them unlimited backdoor access. They were able to access Yahoo’s backup databases and made away with confidential information such as names, emails, passwords, and password recovery questions and answers.
State-sponsored attacks: There have been many cases of state-sponsored attacks. One hundred and forty-four universities within the United States were attacked in 2018 using different types of attacks. The attacks were executed over three years and led to the loss of intellectual properties amounting to $3billion and at least 31 terabytes of data[3]. Investigations revealed that Iran was behind the attack. The United States identified and prosecuted nine hackers of Iranian descent.
Similarly, there have been many other cases of state-sponsored attacks. In 2014, North Korea sponsored the Lazarus Group which hacked into Sony. The hackers released videos of upcoming films and actors’ images. More so, Lazarus has struck other countries targeting their financial institutions. Lazarus’ biggest heist was the Bangladesh Bank attack where the group stole more than $80 million[4].
Gmail and Yahoo attacks: Iranian hackers were able to successfully hack into the Gmail and Yahoo accounts belonging to top US activists, journalists, and government officials in 2018. After studying the habits of the targets, the attackers used spear-phishing emails to trick them into inputting their login credentials in dummy pages accessible by the hackers. The hacks even overcame the highly acclaimed two-factor authentication techniques.
Cybersecurity in the future

Understanding the history of cybersecurity gives you an overview of how cybersecurity has evolved from once being simple experiments and academic research. Cybersecurity efforts now attempt to stop devastating attacks. Current statistics indicate cybersecurity prevalence will continue growing. Cybercriminals are expected to use new innovative strategies for executing stealth attacks by leveraging emerging technologies like artificial intelligence, blockchain, and machine learning.
Besides, as the recent cyberattacks have shown, attackers are capable of bypassing recognized security controls like two-factor authentication. Such attacks show that we still have a long way before we can ultimately become cyber secure. Organizations and security companies have to rethink their approaches towards cybersecurity.
Cybersecurity in the future means that researchers and security experts need to direct all their efforts towards leveraging the benefits of emerging technologies. They must reduce cyber-attack incidences and minimize their effects whenever they occur.
Currently, artificial intelligence is integrated into antivirus and firewall solutions to achieve smarter detection and response capability. Moreover, since all organizations have automated most of their processes, cyberattacks are more concerned with compromising system security. The intent is to prevent them from accomplishing normal operations by locking out system users or stealing critical data.
The emergence of 5G networks is set to automate critical infrastructure like transportation — advances in technology propel cyberattacks to evolve.
We need to anticipate these advances by actively developing countering solutions.
[1] https://www.coloradotech.edu/degrees/studies/information-systems-and-technology/cybersecurity-history
[2] https://www.nytimes.com/2017/10/03/technology/yahoo-hack-3-billion-users.html
[3] https://www.wired.com/story/iran-cyberattacks-us-universities-indictment/
[4] https://www.wired.com/story/iran-cyberattacks-us-universities-indictment/

