The music industry is undeniably becoming a prime target for sophisticated cyberattacks. The intersection of creativity and technology in this field presents unique vulnerabilities for artists, producers, and consumers alike. Whether it is the unauthorized copying and distribution or acts of cyber espionage leading to considerable financial and reputational damage, the threats are multifarious and complex. The endeavor of this discussion is to scrutinize these threats, comprehend their impacts on various stakeholders, and to explore the various cybersecurity measures presently in use. It also aims at projecting the future direction of cybersecurity in the music industry amidst the ever-evolving cyber threats and technological advancements.
The Importance of Cybersecurity in the Music Industry
The inexorable integration of digital domains into every aspect of life has brought with it a myriad of conveniences, but also a corresponding surge in cybersecurity threats. This concern is no less applicable or urgent in the music industry, where its livelihood depends on the secure transmission, storage, and access to digital content. Delving further into the marrow of this topic, we uncover the rationale behind the paramount importance of cybersecurity in the music industry.
Copyright infringement and data breaches are the two main cybersecurity threats to the music industry. Both threats, albeit distinct, can lead to substantial financial losses and compromise the integrity of artists’ creative output.
Copyright infringement, particularly through illegal downloads, proliferated in the early days of the digital music revolution and still poses considerable risk today. Herein lies the first rationale: ensuring that the creative exploits of artists are protected, that they accrue the profit rightfully entitled to them, and that the industry at large retains its economic viability. Cybersecurity solutions aim to avert illegal downloads and streaming, putting effective digital rights management systems in place. Such methods are instrumental in maintaining the music industry’s economic stability.
The second prevailing threat, data breaches, directly affects individuals and organizations within the music industry. Managers’ and artists’ personal information, financial data, unreleased music files, and fan data are all kept digitally and thus can fall foul to the internet’s dark underbelly: cybercriminals. The violation of artists’ and customers’ privacy through data breaches can erode trust, tarnish reputations, and incite legal complications, not to mention the stress and potential trauma it can inflict on affected individuals.
The evolution of music consumption, from physical records to digital downloads and now to streaming platforms, has increased the vectors for potential cyber-attacks. As the music industry grows increasingly dependent on digital platforms, attention and resources must be allocated to guard against these potential cyber threats. Cybersecurity measures function as a gatekeeper, protecting the industry’s most valuable assets – the music and the community of creators, collaborators, and consumers who keep it vibrant.
The integrity of the music, the lifeblood of human expression and connection is kept secure through robust cybersecurity measures that continuously adapt and respond to ever-evolving threats. Thus, it is safe to conclude that cybersecurity is not a luxury add-on in the digital music industry landscape; rather, it is an essential, breathing component – a bulwark that preserves the industry’s vitality in the face of relentless digital challenges.
Types of Cyber Threats in the Music Industry
Delving deeper into the vast panorama of cybersecurity threats in the music industry, it’s crucial to spotlight the ever-increasing specter of malware attacks. Malware, malicious software designed to cause damage, frequently targets the music industry due to its expansive user information database and valuable unreleased content. It encompasses various forms, including ransomware, a particularly destructive form of malware that encrypts sensitive data and demands a ransom for decryption. The now-infamous 2017 NotPetya ransomware attack exemplifies its potential for destruction, shutting down systems across the globe and reportedly causing over $10 billion in damages, interrupted services, and lost productivity.
Expanding further, cybersecurity threats in the music industry are no longer confined solely to the digital arena. The Internet of Things (IoT) is another burgeoning frontier for potential threats. The intensifying integration of IoT devices in the industry, ranging from smart speakers to wearables, have created more pathways for cybercriminals to exploit. The inherent vulnerability of these devices, often lacking in rigorous security measures due to their relatively new presence in the market, can contribute to system breaches and data leaks.
Artificial Intelligence (AI) has transformative impacts across various sectors and plays a dualistic role as a potent cybersecurity threat. Deepfakes, AI-generated synthetic media in which existing images or videos are replaced with someone else’s likeness, pose severe potential threats to artists’ reputations and intellectual property. Concerns loom high as these deep fakes become indistinguishable from reality, thereby further escalating the need for stringent digital safeguards.
Social engineering represents further cybersecurity concerns, manipulating individuals into divulging confidential information. Phishing attacks, a form of social engineering in which emails appear to be from reputable sources and coax users into revealing sensitive information, have seen a surge and show no signs of slowing down. These threats can have negative repercussions far beyond financial losses for an industry heavily reliant on public image and fan-artist interaction.
Given these multifaceted, continually evolving threats, it becomes evident that the music industry’s reliance on digital platforms necessitates a proactive rather than reactive approach to cybersecurity. Emphasizing user education, implementing robust security infrastructure, fostering cooperation fends off cybercriminals protecting against existing threats while preempting new ones. Security isn’t just an add-on for this industry, but a crucial embed into its very functionality and continuity. As we gaze into the future, it becomes clear that the lifeline of music, its creators, its consumers, and the industry itself is closely entwined with the persistent and vigilant application of cybersecurity measures.

Impact of Cyber Threats on the Music Industry
In addition to aforementioned vulnerabilities, at the heart of the music industry lies a persistent cyber threat beyond copyright-beaches and data-infringements: malware attacks. These software intrusions are specifically designed to damage or disrupt systems, often subtly infiltrating software networks undetected before causing widespread chaos. Given the extensive digital distribution and streaming platforms now governing the music industry, the impact of such attacks can be calamitous for both industry stakeholders and consumers.
Ransomware, a particularly formidable type of malware, adds an additional layer of intricacy by holding victim’s data hostage and encrypting crucial files until a ransom is paid. This form of cybercrime has an alarming impact on the industry, as evinced by the notorious NotPetya ransomware attack of 2017, during which massive logistical networks of major industry players were paralyzed, causing millions of dollars in damages.
The proliferation of the Internet of Things (IoT) within the music industry has also intensified its vulnerability to cyber threats. IoT devices, such as smart speakers and musical instruments, create new surface areas for attacks and offer nefarious individuals alternative routes to breach systems and leak data. As these devices become increasingly widespread, sophisticated cybersecurity measures are paramount.
Artificial Intelligence (AI), while instrumental in propelling the industry forward and revolutionizing various aspects of music creation and consumption, also presents a looming cybersecurity threat. Deepfakes, created by using AI to falsely represent reality, can subvert artists’ reputation, diminish their credibility, and infringe upon intellectual property rights, creating a profound and lasting impact on the industry’s dynamics.
Social engineering, which is deceptively simple yet devastatingly effective, is another alarming cybersecurity threat. Phishing attacks empathically highlight the power of manipulated trust. These duplicitous strategies deceive users into divulging sensitive information, emphasizing that the most significant weaknesses in cybersecurity are human, not technological.
It is not, therefore, enough to solely deploy a defensive strategy against these escalating cyber threats. A proactive approach to cybersecurity is the sine qua non of the music industry in the digital age. While robust security infrastructure forms the backbone of this approach, user education cannot be overlooked. If each individual within the broader ecosystem, from artists and producers to consumers, understand their role in maintaining cybersecurity, it would provide an additional line of defense against relentless cyber threats.
Various facets of the music industry, including its functionality and continuity, are reliant on a holistic approach to cybersecurity. Every sector, from the creativity of the artists to the enjoyment of the consumers, can only thrive in a secure digital landscape. Ultimately, cybersecurity in the music industry is not optional; it’s vital and inextricable. Without apt safeguards in place, the industry would be an alluring target, perpetually at the mercy of lurking cyber threats.
Cybersecurity Measures in the Music Industry
Indeed, the proliferation of digital tools and platforms in the music industry brings unprecedented opportunities for creativity, distribution, and consumption – all encapsulated in a sphere of imminent cyber threats. Moving beyond simplistic, defensive tactics, the industry now recognizes an all-inclusive, proactive approach to its cybersecurity strategies.
Irrefutably, cybersecurity measures are no longer just IT department’s concerns, rather they are critical business priorities. The music industry’s cybersecurity strategies today encapsulate a broad spectrum of proactive and reactive measures, incorporating both sophisticated technologies and basic user education.
One significant strategy involves vulnerability management. System administrators are continually scanning for vulnerabilities and weaknesses in the systems deploying globally accepted frameworks like Common Vulnerability Scoring System (CVSS). Once vulnerabilities are identified, these are immediately addressed to reduce opportunities for system infiltration.
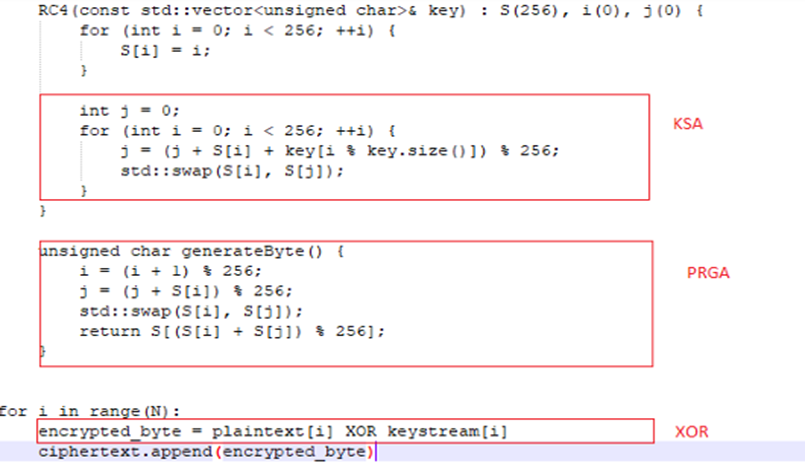
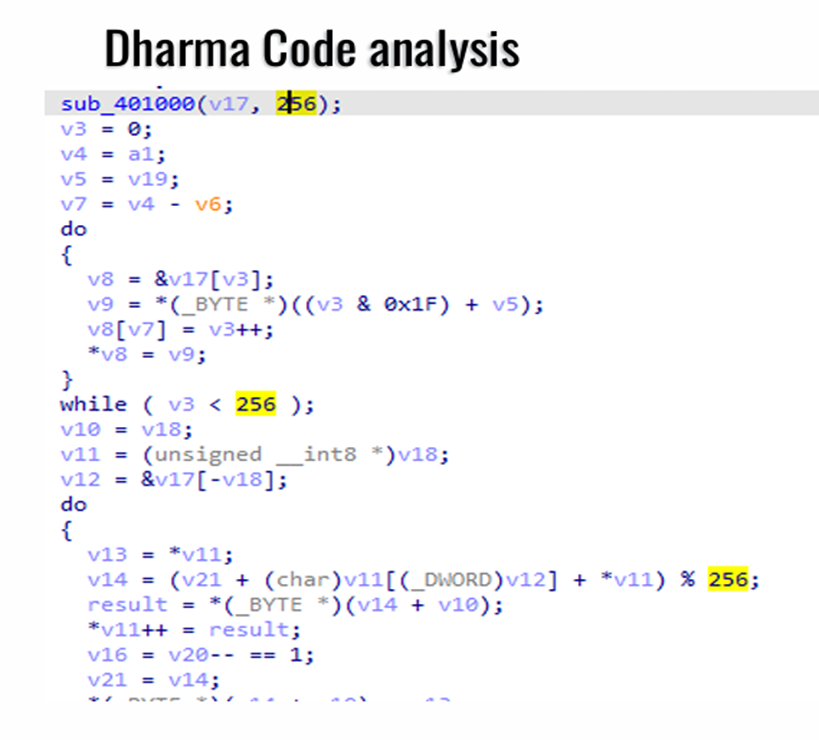
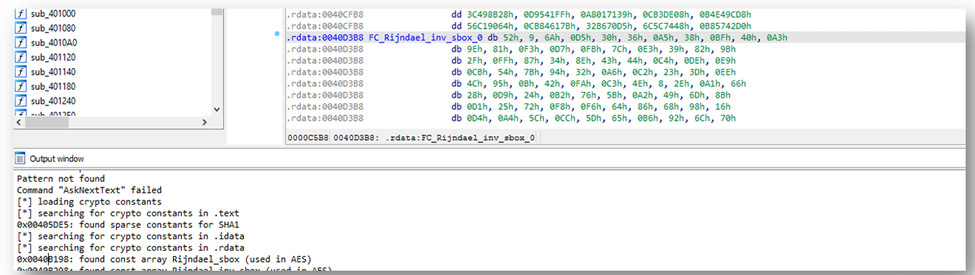
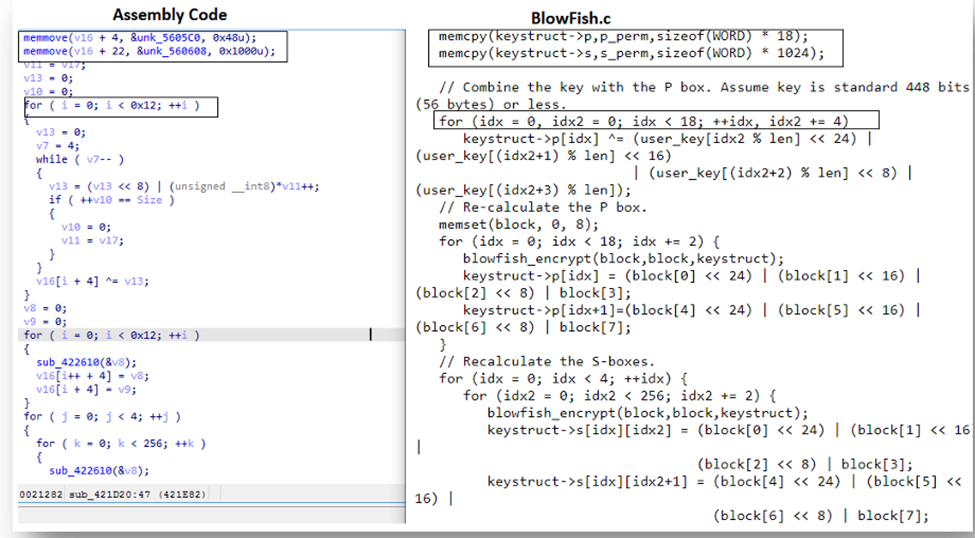
Next, the encryption of sensitive data remains paramount. To counteract the possibility of data breaches and unauthorized access, music companies are routinely using cryptographic protocols like SSL/TLS for communication security over a network, securing both data-in-transit and data-at-rest.
Another major area of focus is on building secure software development processes. Secure coding practices are being adopted to eliminate security vulnerabilities at the development stage itself. The industry is essentially dedicated to keeping the hands of cybercriminals off the software, thus preventing them from exploiting these vulnerabilities, for instance in IoT devices.
AI and Machine Learning (ML) are equally being harnessed in the fight against cyber threats, a measure that could be considered ironically paradoxical given that AI is also a point of vulnerability. AI/ML tools help predict potential threats and detect unknown risks by recognizing patterns and anomalies in real-time, thus accelerating threat detection and response time.
Organizations are also creating incident response teams—a group of experts who conduct regular reviews of security incidents and manage security risks. Their role is also to respond effectively in case of a cyberattack, thus curbing losses and restoring normalcy.
Aside from these technical measures, user education is amongst the most potent preventive mechanisms. Employees are educated about the importance of basic cybersecurity measures, like setting strong, unique passwords and being vigilant about potential phishing attacks. Additionally, consumers are being educated about the importance of legal downloads to combat copyright infringement.
Furthermore, the industry is augmenting its regulatory compliances and addressing cybersecurity risks via comprehensive, industry-specific legislation. Laws like the Digital Millennium Copyright Act (DMCA) have provisions to shield those providers who implement specific safety measures against copyright infringement claims.
Overall, the music industry’s synergistic approach towards cybersecurity is leading to immense progress. However, given the evolving nature of cyber threats, remaining agile and open to future advancements in protective measures is of utmost importance to maintain the rhythm of the music industry’s digital symphony.
Future of Cybersecurity in the Music Industry
As the digital revolution unfurls, it’s clear the music industry has the unenviable task of keeping up with the rapid pace of technological change, especially in terms of cybersecurity. Seismic shifts in technology have completely overhauled both the consumption and production of music, leading to a proliferation of digital tools, platforms, and services that facilitate creativity, distribution, and consumption. Embattled with these opportunities are grave challenges – cybersecurity threats being a chief concern among them.
Navigating this digital landscape mandates the adoption of proactive cybersecurity strategies. The industry needs to move beyond simplistic, defensive tactics, to ensure that cybersecurity is not just an afterthought but an integral part of strategic planning and business continuity. This signifies a shift from considering cybersecurity merely an IT issue to recognizing it as a paramount business priority that deserves complete attention at all corporate levels.
Vulnerability management becomes crucial in this scenario. To foreshadow the potential cyber threats, exhaustive and regular scanning for weaknesses is an imperative catalyst to robust cybersecurity measures. Moreover, the encryption of sensitive data augments the security of technological communication within the industry, shielding it from nefarious activities that might be detrimental to the flow of creative content.
In the realm of software development, security must be a foundational element. A secure software development life cycle can significantly assist in eliminating vulnerabilities that cybercriminals could potentially exploit. Additionally, due consideration must be given to emerging technological solutions such as Artificial Intelligence and Machine Learning. These technologies can be harnessed to enhance threat detection and response, thereby fortifying the cybersecurity infrastructure of the music industry.
Emergencies demand the existence of incident response teams that can manage security risks efficiently, minimizing the impact of potential breaches. While often overlooked, user education on basic cybersecurity measures is of equal importance. Awareness about phishing scams, secure password practices, and the dangers of insecure networks can go a long way in minimizing cyber threats.
The music industry must also augment regulatory compliances, addressing cybersecurity risks through comprehensive legislation. As part of this strategy, promoting legal downloads will combat the rampant problem of copyright infringement, thereby contributing to the economic stability of the industry.
In conclusion, cybersecurity in the music industry requires a dynamic and comprehensive approach. It requires the careful navigation of digital opportunities and threats, all while ensuring protection against cyber-attacks. As the industry pushes the boundaries of creativity, distribution, and consumption, these advancements in protective measures will continue to play a key role. After all, as we stride forward into this thrilling digital age, the music must play on.
As the future unfurls, the music industry is poised for transformative strides, powered by technology. But along with the remarkable possibilities, come unprecedented challenges in the form of complex cyber threats. The role of robust cybersecurity measures thus becomes an unavoidable requisite to shield the industry. Technology, legislative interventions, and proactive measures will form the cornerstone of this protection framework. Artists, industry stakeholders, and lawmakers need to join hands to create a secure digital music landscape that encourages creativity while curbing piracy and copyright infringement. It is only through such a collaborative approach that the music industry can look ahead at a future where the performance that truly counts is not just on the stage, but also on the digital defensive front.