With the growing popularity of e-commerce stores, which offer an easy shopping experience for customers, comes the need to have a more fitting website to connect with your audience. Joomla is a CMS (content management system) platform that you may want to use to build your online store. In addition, it has many e-Commerce extensions, which make it easier to build your site.
Is Joomla Safe from Hackers?
The question of whether or not Joomla is safe for e-commerce stores has been a concern since the emergence of POS (point of sale) malware and cyberattacks on small businesses.
Joomla is not entirely safe from hackers. When it comes to security, it is still a complex system with many vulnerabilities like cross-site scripting, which you may need to understand to fully secure your Joomla website.
Joomla websites often get hacked, and the audiences have no way to know about it because owners don’t communicate it upfront in their terms and conditions. But if we look at the reasons behind it, only two things come out as possible explanations.
The first one is that owners neglect the Joomla website security best practices, for example, by not keeping them up-to-date, and a few don’t even know how to secure their Joomla websites. The second reason could be that they do update but still leave loopholes for hackers to enter.
How you store, data can make your website vulnerable or resistant to online attacks. In this article, we explore common vulnerabilities in Joomla and provide actionable tips on best securing your Joomla website.
Outdated Joomla Plugins, version, and extensions
The first step in securing a Joomla website is to update your Joomla components. To do so, go to the Components page and select Check for Updates.
This will notify you if there are any available updates or not. If yes, then it’s wise to proceed by clicking on Install Updates, which will remove all the old and outdated components from your Joomla website.
In installing the updates, it is also essential to remove any extensions that you no longer use because they may still be vulnerable or have a security hole that hackers might exploit for their purpose. This can only be done by going through each extension and unchecking the ones you no longer require.
Restrict Access to Joomla Admin Backend
This is an essential step for Joomla store owners because it will prevent hackers from accessing the backend of your website. You will need to change the default Joomla administrator URL which is usually; http://www.yoursite.com/administrator.
There are free Joomla extensions you can use to change the default admin URL. A relatively common option you may want to use is the AdminExile plugin. When restricting access to ensure that you have a secure Joomla website, it is also prudent that you change the default Username/Password.
Update Joomla Database
It is also essential to update the database and make sure it’s secured with a strong password. The username and password for the MySQL database can be changed by going to Components > Secure MySQL Access from the bottom right-hand corner of the screen. Next, select your username and password from the Secure MySQL Access window options and click on Secure Connection.
This will encrypt your Joomla database with a strong password and make it difficult for hackers to steal any information about your website. On the same note, if you want to update the username and password of the MySQL database, then go back to the Components page and select Secure MySQL Access from the bottom right-hand corner of your browser.
Next, select Secure MySQL Access and then click on the Secure Connection button. This will encrypt the Joomla database with a strong password and make it difficult for hackers to steal information about your website.
Install an SSL Certificate
It is also essential that you get an SSL certificate for your website. Secure Socket Layer (SSL) encrypts the in-transit data between the web browser and server, which helps protect sensitive information like credit card numbers during online transactions.
This will encrypt all your data sent across networks, making it difficult for hackers to steal any information about your website. If you have just one domain or subdomain to secure, you can buy a cheap positive SSL, and that will do the job.
However, Joomla e-commerce website owners often have multiple first-level subdomains such as product pages, blogs, payment pages under one primary domain. Therefore, it doesn’t make sense to invest in separate single-domain SSL for each new subdomain that they add.
In this case, we strongly recommend going for a wildcard SSL certificate. Looking for cheap yet premium wildcard options? Well, you can buy Rapidssl Wildcard and afford premium encryption to your chosen primary domain and unlimited first-level subdomains at meager costs!
Set Strong Passwords
You must use a strong password for your Joomla administrator account. While this is not technically related to securing the Joomla website, it will help keep hackers from hacking into your admin console and then doing any damage. So, make sure that you don’t set the same password as before or something easy like 123456.
Use Joomla Two Factor Authentication
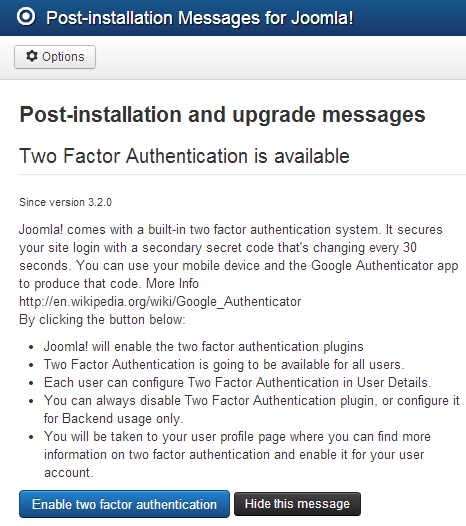
If you want to restrict the access of your Joomla admin console and reduce any chances of a hacker breaking into it, then use Two Factor Authentication (2FA) for maximum security. This will ensure that all users need two pieces of information – username and password or 2FA token- to log in.
This provides added protection from hackers who might have compromised authentication credentials. They would also require an additional piece of information like an SMS text message or an app notification on their phone with a one-time code before being allowed inside your website’s backend.
Joomla 2FA is available for Joomla versions 3.2.0 and above. To enable the Joomla Two Factor Authentication on your Administrator Panel, go to Components -> Post-Installation Messages and then select Two Factor Authentication. You will be redirected to the user profile page.
Proceed to install the Google Authenticator Client->Scan the QR code with your phone->key in the generated 6-digit code->click on ‘Save & Close.’
Use a Joomla Web Application Firewall
For ultimate security, you can install a Joomla Web Application Firewall (WAF), an application that protects web servers from malicious activity like SQL injections and cross-site scripting. Configure WAF to monitor incoming traffic to detect any suspicious requests or even attacks on your website.
Take Regular Backups
It is also a good idea to take regular backups of your Joomla website. This will help you recover from any disaster or hacking attacks if something goes wrong with your site by having an up-to-date copy that can be restored.”
Choose a reliable Hosting Provider.
Do note that your hosting provider also has a hand on how secure your Joomla website can be. Therefore, you must choose a reliable hosting provider for your website. A secure Joomla website should be hosted on web servers with security in mind and one which will take care of all the technical details to make sure your site runs smoothly.
In Closing, having a secure Joomla website could mean the difference between having a successful and profitable eCommerce store or one that suffers from high-profile data breaches. So, act now to secure your Joomla website and enjoy peace of mind from knowing that your data is safe and sound.

















