Summary
- Artificial Intelligence (AI) and resilience are increasingly pivotal in shaping the cybersecurity landscape’s future.
- Key players are focusing on integrating AI to enhance threat detection and response capabilities.
- Cybersecurity innovation is essential to protect critical infrastructure and anticipate evolving threats.
- Challenges persist in balancing rapid innovation with security protocols.
Introduction
As the digital realm continues its relentless expansion, the fusion of AI and resilience within cybersecurity is proving to be a game-changer. Amidst the wave of technological advances, these components are not just complementary but essential in redefining the armor that shields critical infrastructure from an ever-evolving threat landscape. This article explores the intricate dance of AI-enhanced cybersecurity strategies and how they are setting the stage for future innovations.
The Role of AI: Elevating Cyber Defenses
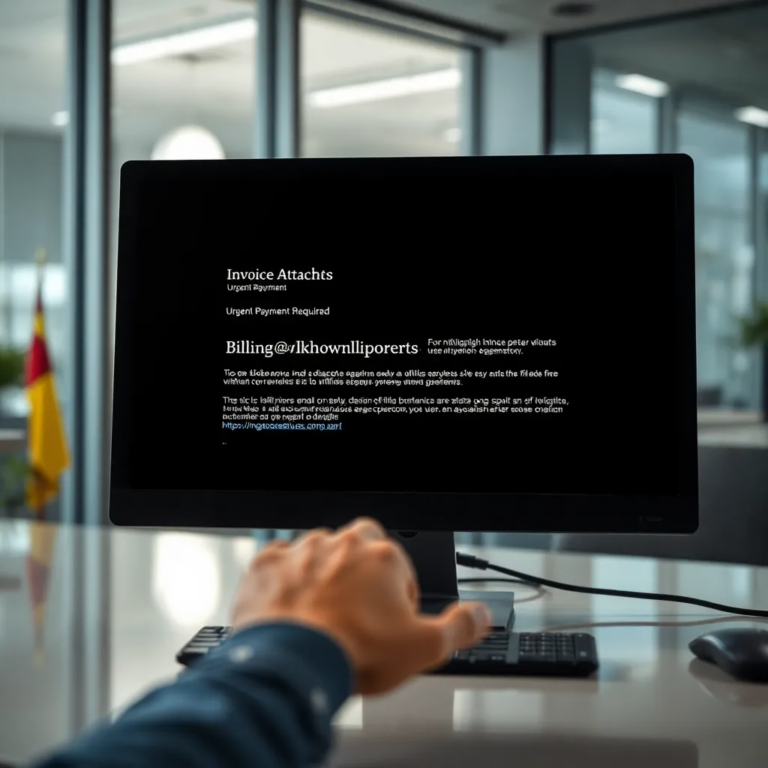
The integration of AI into cybersecurity solutions is rapidly transforming how threats are detected and neutralized. AI’s capacity for processing vast amounts of data at remarkable speeds allows for the swift identification of anomalies and potential threats. Leading companies are harnessing this power to build more responsive and anticipative security protocols. According to experts, AI not only bolsters automated defenses but also augments human analysts by filtering out false positives, thereby enhancing the overall efficiency of security teams.
Resilience as a Core Principle
In the bustling world of cybersecurity, resilience is not merely a buzzword but a foundational philosophy. The ability to withstand, adapt, and recover swiftly from cyber incidents is crucial. Increasingly, firms are embedding resilience into their organizational DNA, ensuring that systems are designed to minimize disruption and maintain functionality under duress. This shift towards a resilience-oriented approach is driving both strategy and innovation, emphasizing speed in recovery and adaptability as key characteristics of robust security frameworks.
Challenges and Innovations
Innovation within cybersecurity is essential but laden with challenges. The rapid pace of technological development must be judiciously balanced with stringent security protocols. The temptation to prioritize innovation over security can lead to vulnerabilities. Nevertheless, key players in the industry are pioneering solutions that integrate security from the ground up. Continued efforts in research and development are vital for advancing these duel goals of innovation and protection.
Key Players Shaping the Future
Companies operating at the intersection of cybersecurity, AI, and resilience are poised to shape tomorrow’s digital defenses. These industry leaders are not only developing groundbreaking technologies but also pioneering strategies that redefine security measures. Their role in sculpting a resilient digital ecosystem is pivotal, ensuring that the threats of tomorrow are met with robust and adaptable defenses.
Conclusion
The convergence of AI and resilience is revolutionizing the cybersecurity field, paving the way for an era of heightened security awareness and advanced threat management. As these elements become ingrained in the DNA of cybersecurity solutions, they offer a promising glimpse into a future where digital safeguards are as dynamic and adaptable as the threats they aim to counter. Stakeholders across industries must remain vigilant, continuously striving to refine and enhance their security posture in the face of inevitable shifts in threat dynamics.