FCC Targets Undersea Cables: New Cybersecurity Rules to Shape Connectivity
Summary
- The Federal Communications Commission (FCC) is reevaluating cybersecurity mandates for undersea cable operators.
- The initiative aims to safeguard global internet connectivity from cyber threats.
- Public input is being sought in shaping the new regulatory framework.
- Strategic measures include enhancing transparency and response to cyber incidents.
Introduction
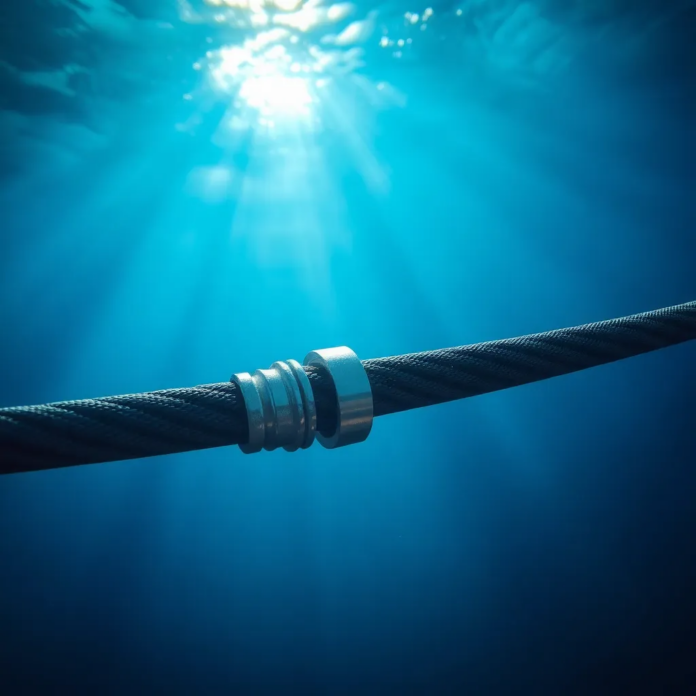
Submarine cables lie at the core of the world’s internet infrastructure, transmitting over 95% of international data traffic. The Federal Communications Commission (FCC) is focusing on enhancing the cybersecurity landscape of these vital conduits. With the increasing dependency on digital communication, these cables are more crucial than ever but also vulnerable to cyber threats. The new proposed rules by the FCC aim to solidify the defenses of these critical infrastructures.
Revamping Cybersecurity Protocols
The FCC’s Proposed Initiatives
The FCC’s proposal marks a significant shift in how submarine cable operators approach cybersecurity. Central to this initiative is the requirement for operators to adopt detailed measures assessing the security of their operations. This means developing robust systems for detecting and responding to cyber intrusions, as well as maintaining records of all significant cybersecurity incidents.
Need for Updated Security Measures
The current geopolitical climate and the rising sophistication of threat actors necessitate enhanced cybersecurity frameworks. Undersea cables, often perceived as secure, face risks that could have far-reaching consequences if not adequately addressed. The FCC acknowledges that an incident affecting these cables can disrupt not only communication but also economic activities globally.
Stakeholder Engagement: Seeking Public Input
The FCC recognizes that public engagement is essential in formulating effective policies. By opening the review process to public comment, the commission aims to gather insights from a diverse range of stakeholders, including industry experts, academic institutions, and national security agencies. This participatory approach ensures that the rules are comprehensive and practical.
Implications for Global Connectivity
The broader implications of this initiative are substantial. With a push towards more stringent regulations, submarine cable operators may need to invest significantly in new technology and training programs. However, experts argue that the long-term benefits—such as improved reliability and heightened security of global communications networks—justify these initial investments.
Enhancing Transparency and Response
A pivotal aspect of the proposed rules involves improving transparency and response capabilities. Operators will be required to implement communication protocols that promptly notify relevant stakeholders of any cyber incidents. This will help minimize the impact of disruptions by facilitating quick remedial actions.
Conclusion: Shaping a Secure Future
As the internet’s backbone, submarine cables require robust defenses. The FCC’s initiative is a proactive measure aiming to secure this critical infrastructure against growing cyber threats. By seeking public input and focusing on comprehensive security requirements, the FCC is not only addressing immediate vulnerabilities but also paving the way for a secure and reliable future for global internet connectivity. With these new measures, the FCC sets a precedent for international telecom regulatory bodies, emphasizing the collaborative effort needed to protect the very veins of our digital age.
In an era where connectivity drives economies and links societies, ensuring the security of undersea cables is not just a national concern but a global imperative. The FCC’s proposed regulations signal a commitment to strengthening the cyber resilience of the networks we rely on daily.
Want to know how these risks apply to your business?
Get an AI Cyber Checkup and receive a practical AI-generated action plan showing what to fix first.
Get an AI Cyber Checkup