This discussion delves into an exploration of the various cyber threats, outlining their mechanisms and their potential impacts. Moreover, aiming to safeguard yourself and your digital assets, we comprehend the fundamental protective practices like Virtual Private Networks (VPNs) firewalls, enforcing regular system updates, constructing strong passwords, and implementing user privileges. Taking it a step further, an introduction to cybersecurity tools and software will provide a practical approach to secure digital environments, shedding light on their types and uses – encompassing antivirus software, encryption software, and network scanning tools.
Understanding the cyber threats
Headline: The Common Forms of Cyber Threats: A Comprehensive Breakdown
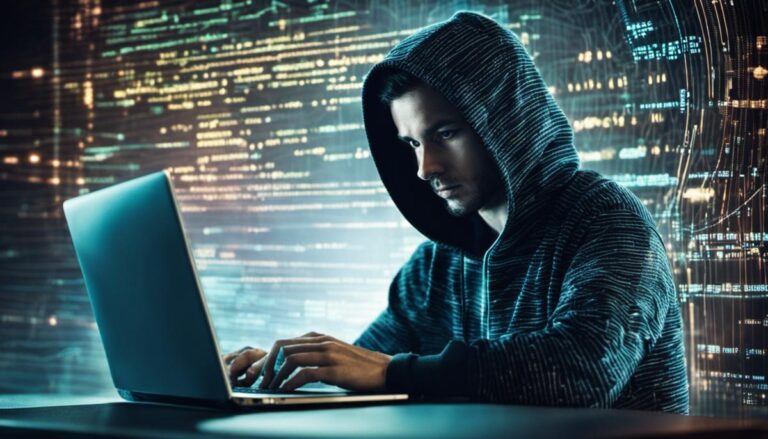
The rapid growth of technology across the globe has opened up a new set of risks in the realm of cybersecurity. In the face of these increasingly sophisticated cyber threats, it makes sense to stay informed about the different forms they can take. Here is a brief examination of the common types of cyber threats from an enthusiast’s perspective.
-
- Data Breaches
Data breaches are among the rampant cybersecurity threats today. They occur when unauthorized individuals gain access to confidential data, such as financial and personal details. Major corporations, healthcare institutions, and even government agencies have fallen victim to data breaches, resulting in considerable financial losses and privacy risks.
Phishing attempts are designed to trick individuals into revealing sensitive information, such as passwords and credit card details. Cybercriminals often achieve this by impersonating trustworthy entities through emails or text messages. Clicking on a link or opening an attachment in a phishing email can lead to data theft or damage.
-
- Ransomware Attacks
Ransomware attacks are rapidly growing in prevalence. The attacker encrypts the victim’s data and demands a ‘ransom’ to restore access. These attacks can cripple businesses by locking down essential systems and files, causing severe disruption to operations and potential financial ruin.
Malware, an umbrella term for malicious software such as viruses and worms, functions by infiltrating the victim’s system without consent. It can cause harm by deleting files, harvesting personal information, and even taking control of the system’s operations.
-
- Denial of Service (DoS)
A DoS attack overwhelms a network or a website with traffic, causing it to be slower or even completely inaccessible. Even though the attacker doesn’t gain direct access to data or systems, such attacks can cause significant downtime, leading to financial losses and damaged reputation.
-
- Man in the Middle (MitM)
In a Man in the Middle attack, the cybercriminal intercepts communication between two parties to steal or manipulate the data. MitM attacks are commonly executed on unsecured public Wi-Fi networks, allowing cybercriminals to capture sensitive information.
With an understanding of these common forms of cyber threats, it’s evident that the indispensable role of robust cybersecurity measures can’t be emphasized enough. Adequate knowledge coupled with critical security practices like secure coding, regular software updates, data encryption, and the usage of antivirus software can be the first strides toward maintaining a resilient digital environment.
Basic preventive practices
Proactive Steps to Staying Ahead of Cyber Threats
Understanding the nuances of cyber threats and knowing how to protect against them effectively can seem like a daunting task, yet it remains an indisputable necessity given the rapidly expanding digital terrain of modern life. Regardless of whether one is a casual web surfer, a tech enthusiast, or a corporate giant, cybersecurity should be a fundamental focus. So, what more can be done to fortify digital defenses beyond the measures already listed? Let’s delve in.
Establish A Strong Firewall
A firewall acts as the first line of defense against potential cyber threats. It monitors incoming and outgoing web traffic, blocking suspicious activities and ensuring high levels of security. This barrier helps to prevent unauthorized access, warding off hacker intrusions, viruses, and other malicious threats.
Embrace Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security during login processes. Typically, it involves the user providing two different authentication factors, such as a password and a unique code sent to their mobile device. This extra verification step can drastically reduce the feasibility of unauthorized account access.
Educate & Train Yourself and Your Team
Knowledge is power, and this holds true in the realm of cybersecurity. Understand how cyber threats work and stay updated on new and evolving techniques. Regularly share this information with team members to create a culture of cyber vigilance.
Avoid Suspicious Emails & Websites
While it sounds obvious, it bears repeating because of its practical importance: steer clear of suspicious emails and websites. Be on the lookout for dubious links, email addresses, and attachments. Careless clicking leads to significant security breaches.
Use a Virtual Private Network (VPN)
A VPN establishes secure, encrypted connections, providing more privacy than a secured Wi-Fi hotspot. This can make it extremely difficult for cybercriminals to access your data.
Develop Secure Password Policies
The strength of a password can often be a defining factor in preventing unauthorized access. Aim for complex, unique passwords and change them regularly. Consider using a reputable password manager to handle this task.
Back up Important Data Regularly
In the unfortunate event of a cyber attack, data loss can be devastating. Regularly backing up important data can mitigate potential damages in such situations.
It merits repeating that the world of cyber threats is ever-evolving. Today’s solutions may not suffice for the problems of tomorrow. Therefore, constant updating of knowledge and adapting of strategies is of paramount importance.
Remember, your digital playground can instantly transform into a battlefield. Stay aware, stay updated, and stay safe.

Introduction to cybersecurity tools and software
With the previously discussed aspects of cybersecurity, such as data breaches, phishing, malware, and robust security measures in mind, there are additional essential tools and practices required to ensure your digital sphere’s security. Being proactive in implementing these strategies will help to develop a comprehensive shield around your sensitive information.
Firstly, the role of Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) cannot be overlooked in cybersecurity. IDS helps in identifying any malicious activities on your network while the IPS prevents detected threats from entering. Advanced systems even have machine learning capabilities that enable them to adapt and respond effectively to new types of attacks.
Next, the importance of regular vulnerability scanning should not be underplayed. Vulnerability scanning tools assess your network or software for weak points that hackers could exploit. By conducting regular scans, potential loopholes can be promptly detected and fixed, therefore keeping your system a step ahead of potential attackers.
In addition to these, Web Application Firewalls (WAFs) are necessary to ensure secure interactions on your website. By filtering and monitoring HTTP traffic between a web application and the Internet, WAFs protect your website from attacks such as cross-site forgery, cross-site scripting (XSS), and SQL injection.
Employing a Security Information and Event Management (SIEM) system is another crucial step. SIEM provides real-time analysis of alerts generated by applications and network hardware. It aggregates data, allowing for multiple feeds and logs to be analyzed together for a unified threat analysis.
Don’t forget that mobile devices also require protection. Mobile Device Management (MDM) tools help secure, monitor, and manage the mobile devices used within your organization. They can expedite the detection of compromised devices and take swift actions such as denying access to sensitive data.
Data Loss Prevention (DLP) tools are essential to prevent unauthorized data transfers or leakage. They can either be network-based for protection against online leaks or endpoint-based to assess data in use and at rest.
Last but not least, consider the use of Artificial Intelligence (AI) and Machine Learning (ML) in cybersecurity. These cutting-edge technologies can predict and effectively respond to threats in real-time, continually learning and improving over time. They add an entirely new layer of threat intelligence to cybersecurity strategies.
By diligently utilizing these crucial tools and technologies, a comprehensively protected digital landscape can be created, resilient against evolving threats. Always remember that the stronghold of cybersecurity lies in its evolving nature – being able to adapt and improve is of the utmost importance in staying digitally safe.
And remember: cybersecurity is not a one-time fix but an ongoing, adaptive process that keeps pace with advancing technology trends. It requires constant vigilance and regular updates to keep defenses strong. No one said that it’s an easy task, but in an increasingly interconnected world, keeping your digital environment safe from threats is paramount to your steadfastness in the vast field of cybersecurity.
The complex world of cyber threats and the myriad of preventive measures and tools that exist might initially seem daunting. However, gaining a rudimentary understanding can empower us to navigate digital spaces with increased confidence and security. Cyber threats such as viruses, phishing, spyware, and ransomware can wreak havoc on unsuspecting users, but with basic precautionary practices like VPNs, firewalls, regular updates, strong passwords, and user privileges, the risks can significantly be mitigated. Even more so, with the aid of cyber security tools and software that help to detect, prevent, and combat these threats. As the digital landscape continues to expand and evolve, staying updated and vigilant in regard to cyber security can no longer be an option but a necessity. Recognizing the threats and knowing how to counteract them is the first step toward creating a secure digital world.