Our growing dependency on digital infrastructures is met with a corresponding rise in cybersecurity threats, making that network security system a crucial pillar of our modern world. It is vital for us to understand the cornerstone principles of Network Security Systems, including firewalls, intrusion prevention methodologies, secure access controls, and encryption strategies. Alongside this, we must also be cognizant of the multitude of threats that loom over network security – malware, hacking attempts, phishing scams, and Denial of Service attacks, a testament to both the technical and human vulnerabilities inherent in our systems. This article aims to impart the reader a broad yet detailed understanding of the nuts and bolts of network security, immersing them into the relentless contest between securing digital assets and the persistent onslaught of cyber-attacks targeting those assets.
Basics of Network Security System
Unraveling the Fundamentals of Network Security Systems
In the realm of technology, the constant advancement invariably forces us to up our game. It demands ceaseless vigilance from anyone invested in an ever-connected world. Network security, the fortress between data and threats, stands as an irreplaceable linchpin. Let’s dive into the fundamental elements and principles underpinning an impeccable network security system.
First and foremost, the lifeblood of all network security systems: Firewalls. Acting as protective shields, they filtrate traffic, forming the first line of defense against malicious entities. Firewall rules determine what information can pass through the gates, differentiating between harmful and benign data.
Simultaneously, Intrusion Detection Systems (IDS) work to identify potential threats. By monitoring network traffic and recognizing abnormal activities, IDS swiftly alerts technicians about any potential intrusions. Elegantly dovetailing with firewalls, Intrusion Prevention Systems (IPS) take action on these alerts, blocking or rerouting threatening data before it enters the network.
Then there’s Anti-Malware software. Widely recognized, it quarantines and eliminates hostile software such as viruses, Trojans, ransomware, and spyware. Designed to detect, thwart, and clean infectious programs, this component downs the intruders that somehow manage to slip past Firewalls and Intrusion Prevention Systems.
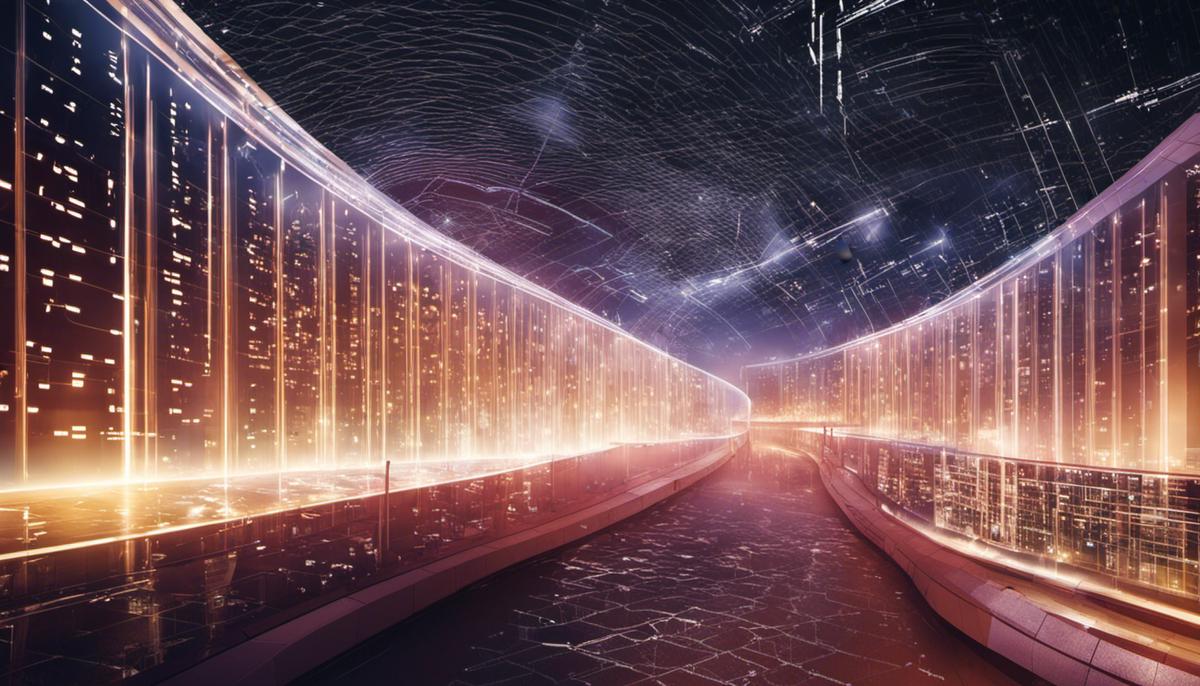
Don’t forget about Virtual Private Networks (VPNs). These create an encrypted tunnel between endpoints, providing a secure conduit for sending and receiving data across public networks. Essentially, VPNs cloak data transfers, making it nearly impossible for any eavesdropper to comprehend the transmitted information.
Another key cornerstone of network security is the Data Loss Prevention (DLP) systems. These tools restrict users from uploading, forwarding, or even printing critical information in an unsafe manner. The goal here is to ensure that sensitive data doesn’t escape the network.
But these are merely defensive tools. An effective network security system also requires proactive measures. Vulnerability scanners come into play here, running scheduled audits over the system. These scanners identify exploitable loopholes before any ill-intentioned entity can find them.
Last but not least, good network security systems adhere to fundamental principles. Confidentiality, Integrity, and Availability, or CIA, provide the basic guiding framework. This trinity ensures that only authorized parties have access to data (Confidentiality), the data is trustworthy and accurate (Integrity), and the information is readily accessible whenever it’s needed (Availability).
Ultimately, network security stands as a crucial arena where technology enthusiasts thrive. It’s all about creating a fortress that is impenetrable by malevolent forces yet still hospitable for valid users. Patching up vulnerabilities, responding to threats, and ensuring data availability by using a combination of intelligent systems is the essence of network security. Jump in now and stay ahead of the curve because the future waits for no one.

Threats to Network Security
Titled: The Hidden Peril in Our Network: Security Threats
If there’s one thing we can’t ignore in our tech-centric existence, it’s the ubiquitous, ever-evolving threats to network security. Beyond the mechanisms and safety nets we all know – firewalls, intrusion detection systems, VPNs and the like – lurks an insidious digital underworld that’s continually probing for vulnerabilities. By automating defenses and staying ahead of the curve with preventive measures, we can effectively fend off these looming dangers. Let’s dive straight into the threats our networks could face today, and what we can do to combat them.
Phishing Schemes:
Cyber criminals excel at exploiting human error, and phishing serves as their primary tool. These crafty attacks disguised as legitimate emails or messages aim to extract sensitive data for malicious purposes. Utilization of strong anti-spam filters, user education, and multi-factor authentication can significantly reduce the risks associated with phishing.
Ransomware Attacks:
Ransomware, an extremely disruptive form of malware, effectively hijacks vital data or systems on your network until a ransom gets paid. This malignant software can prove disastrous without preventive measures such as timely data backups, end-user training, and rigorous anti-malware solutions.
Zero-day Exploits:
These attacks exploit unknown software vulnerabilities before developers get a chance to address them. One could neutralize such threats by keeping all software up to date, using reputable hardware and software vendors, and deploying automated patch management tools.
Insider Threats:
Betrayal from within often eludes firewalls and intrusion systems. Disgruntled employees or ill-intentioned insiders could cause significant damage. Effective countermeasures can involve stringent access control, regular audits, and enforcing the principle of least privilege (POLP).
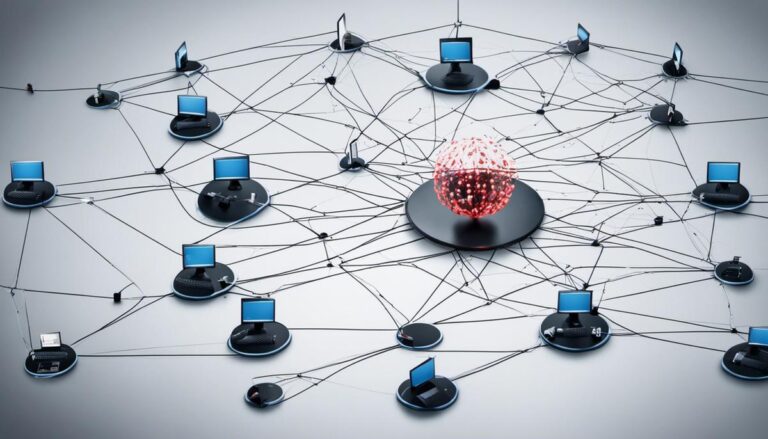
Denial of Service (DoS) Attacks:
These attacks attempt to exhaust your resources, making your network unavailable to legitimate users. DoS attacks typically target your capacity to deal with traffic on web servers. Hardware-based firewalls equipped to handle these attacks and load-balancing measures are effective defenses.
Advanced Persistent Threats (APTs):
Prolonged and targeted cyber-attacks that aim to stealthily infiltrate a network to steal data over extended periods are another emerging threat. Robust cybersecurity platforms, continuous network monitoring, and rapid incident response can mitigate their impact.
Ignoring these threats is not an option in the world we live in, just as much as emerging technologies are not a luxury but a necessity. Automating defenses and incorporating robust, multi-layered security solutions will be key to securing our network future. And remember, always stay one step ahead – be prepared, not scared!
Modern Solutions and Tools for Network Security
The rapid advancement in digital technology is a double-edged sword. While this unprecedented pace of change provides us with countless benefits, it also creates daunting challenges, particularly in the field of network security. Recent innovations, however, provide promising solutions to mitigate risk and strengthen cyber defences.
Emerging importantly in network security faucets is the integration of Artificial Intelligence(AI) and Machine Learning (ML). Providing a proactive approach to identify erratic behaviour patterns – AI and ML algorithms leverage big data analytics to predict potential threats and promptly warn network administrators, offering rapid responses to possible vulnerabilities.
The rise of Blockchain Technology brings significantly heightened security, offering a fascinating solution to data integrity issues. Trailing every transaction and maintaining records across several systems, the blockchain negates the risk of data manipulation and unauthorized access.
Secure Access Service Edge (SASE) is another groundbreaking strategy to boost network security. Unifying networking and security services into a single cloud-based platform, SASE caters to the needs of organizations undergoing digital transformation, backing up their highly distributed networks and mobile workforces while simplifying their wider security architecture.
Yet another innovation is Deception Technology. Modeled to confound would-be attackers, this technology plants fictitious decoys to distract intruders from real network assets, sowing confusion and thereby protecting vital data. Simultaneously, it helps gather intelligence on the intruder’s tactics, offering key insights on improving security measures.
Despite not being entirely new, the role of Biometrics is progressively beneficial in bolstering network security. Two-factor or multi-factor authentication processes, often involving biometric data, add an invaluable layer of protection, making unauthorized access significantly more challenging.
Moreover, the advent of Quantum Networking offers a remarkable breakthrough – a network virtually immune to eavesdropping, given that its state changes when an intruder tries to intercept it. Though presently in its early stage, the potential of quantum computers in network security is immense, and an area to watch closely.
As appealing as these innovations are, they require strict measures to ensure their efficacy. A network’s security strength is only as good as its weakest link. Therefore, regular updates, rigorous testing, and keeping abreast of emerging trends are crucial in bolstering network security.

Future of Network Security System
As the world of technology presses further into the horizon, Network Security Systems must keep apace. This quest ventures beyond the finite realms of firewalls and intrusion detection systems; it moves into the revolving frontier of tech innovation where novelties like artificial intelligence, blockchain, and quantum networking hold the future of network security systems.
These imminent advancements bring significant potential for network security. Artificial Intelligence (AI) and Machine Learning (ML), for instance, are no longer futuristic concepts but the here and now. These forward-looking technologies are predicted to revolutionize network security by proactively identifying and responding to threats in real-time, considerations otherwise unachievable by traditional means. Through AI and ML’s relentless analysis of network patterns and behavioral data, the prospect of identifying unknown risks or ‘zero-day exploits’ is a revolutionary leap forward.
Blockchain technology, well-known for its application in cryptocurrency, also has promising implications for network security. The decentralized nature of blockchain effectively protects data integrity by making unauthorized alterations nearly impossible. Upgrading network security systems with blockchain technology could potentially eradicate issues related to data tampering and provide a robust standard to the CIA principles.
The use of big data analytics has also emerged as a practical solution in predicting and mitigating security threats. By analyzing vast amounts of information rapidly, big data analytics can predict questionable patterns and flag potential security breaches faster than ever before.
Further, the integration of Secure Access Service Edge (SASE), a cloud-based platform, provides comprehensive security services to globally distributed organizations. SASE combines network security functions with WAN capabilities to support the dynamic, secure access needs of digital enterprises, thus substantially reducing the chance of DoS attacks and APT intrusions.
Similarly, deception technology, an innovative security measure, is devised to deceive and thereby confuse attackers, turning their tactics against them while gathering valuable intelligence for future threat prevention. This subtle yet intelligent integration of defense and attack is imperative in the ever-escalating world of cyber threats.
In tandem with the rapid digitalization of industries around the globe, the future also brings authentication processes an upgrade. Biometric identification techniques such as fingerprint scanning, facial recognition, and voice identification not only reinforce network security but also provide a user-friendly alternate to cumbersome password systems.
Moreover, the potential of quantum networking may redefine network security as we know it. Quantum networks, with their ability to form unhackable communication circuits, show great promise in creating a quantum leap in network security.
These future solutions aren’t without their trials. Ensuring the efficacy of these technological wonders will require constant testing, evaluation, and optimization. But, as the digital world expands, the demand for robust and adaptive network security will grow concurrently. Therefore, it is crucial that we continue to pioneer new ways of countering these threats in our quest for a safer digital world. In this unrelenting pursuit, technology emerges both as a challenge and a solution, forever reshaping the landscape of network security systems.
As we journey through the thrilling labyrinth of Network Security System, it becomes starkly apparent how the rate of technological advancement fuels the arms race between security measures and cyber threats. Delving into the existing tools and strategies on offer—including advanced firewalls and AI-driven defenses—offers a snapshot in the current state of our ongoing third-party security blanket. However, it’s equally important to look at the horizon and anticipate upcoming advancements that will shape the future in this increasingly complex sphere. From emerging technologies to innovative, future-proof strategies, the future of Network Security System bears potential for extraordinary strides in progress. The continued evolution in this field would be a testament not only to defensive success but also, symbolically, to our persistent resilience and adaptability in an ever increasingly interconnected world under constant cyber threats.