In the English Poet Jon Donne’s (1624) words, “No man is an island, entire of itself.” This statement is true for nations, corporations, and individuals. In an article about “The Importance of Alliances for U.S. Security” published on Heritage.org, Martin Murphy states that “states of roughly equivalent weights may feel emboldened to pursue riskier foreign policies because their allies are obligated to come to their rescue.” An alliance can be a formal, written treaty or an informal, unwritten agreement based on anything that ranges between tacit understandings and verbal assurances.
The primary goal of any alliance is to advance the members’ collective interests through combining and leveraging their capabilities, such as financial, skill, and military resources. This purpose is based on the fact that no single state or business can provide all capabilities and proficiency needed to accomplish a sophisticated task.
The Age of Cybersecurity Alliances is Nigh
One of the best strategies companies have come up with to curb cyberattacks is to form cybersecurity alliances. Companies come together with a common interest in sharing technical data and intelligence on the ever-evolving cyber threats. Such alliances feature strong public and private partnerships that promote the creation and implementation of measures to empower individuals and organizations to secure their systems and sensitive information online while encouraging a cybersecurity culture.
Why are Companies Warming Up to Cybersecurity Alliances?
In most cases, governments focus on securing companies and citizens in the physical world. However, in the digital space, they are investing in building their offensive capabilities at the expense of keeping companies and individuals safe from cyber threats. This observation can be attributed to the governments’ view that cyberthreats are not impacting a nation’s safety hugely. Unfortunately, the emerging trends in cyberspace (Internet coverage, cloud computing, IoT, cyber-physical systems) and increasing sophistication of cyberattacks make cybersecurity an essential aspect of human safety.
Key players in the digital world realm, such as Samsung, HP, and Siemens, have channeled their efforts to develop cyber threat defense. This is in response to the low involvement of federal protection agencies in cybersecurity. Alliances such as the Global Cyber Alliance (GCA) were formed to bring together vendors and end-users to create an open platform to exchange insights, information, analytics, and event solutions.
When a breach occurs, there tends to be a breakdown of trust between policymakers and customers. Cybersecurity alliances bridge the trust gap. Companies’ tight-knit and compact groups uphold values such as accountability and trust to promote peace among the members. Alliances enable companies to work in harmony towards a common goal of securing a future for digital networking. When these companies work hand in hand, not only are they able to curb threats, but they also stay updated on upcoming or future threats through a pooling of information. Alliances offer an administrative and operational framework that is reliable, flexible, and reflective of cybersecurity market needs.
Types of Cybersecurity Alliances
There are two major types of partnerships in terms of the purpose they serve. Different companies come together and form pacts for various reasons. The aim to which an alliance is created may vary following its members. The two types of partnerships are normative alliances and operational alliances.
1. Normative Alliances
These alliances provide support to companies vulnerable to cyber threats. One of the critical purposes of normative alliances is to seek government support on cybersecurity matters. This involves vouching for a limit on the use of private networks by a state on its citizens. Due to the low government concerns on cybersecurity issues, normative alliances allow companies to draw their line of defense against the threats facing them. Peace and order must prevail among the members for them to work together effectively. Trust is a significant prerequisite ingredient of peace. Normative alliances such as the Charter of trust uphold trust as a key value within the coalition.
Normative alliances are aimed at renegotiating the social contract between state governments and their citizens. Through the sharing of varying tactics of combating cyberthreats, normative alliances change how companies approach these vulnerabilities. Pioneered by Microsoft and other major companies, the cybersecurity accord aims to promote “a safer online world by fostering collaboration among global technology companies committed to protecting their customers and users and helping them defend against malicious threats.” The open letter to the G7 government to prioritize cybersecurity is a step by normative alliances to push the state to apply more concern on digital issues.
2. Operational Alliances
These are based on smaller groups of companies keen on sharing technical data and intelligence on cybersecurity. These member companies share their experience and tactics on cyberattacks and threats. One of the primary reasons companies form operational alliances such as the Cyberthreat alliance and Trusted Computing group is keeping their IT or CISCO departments apprised of current attacks or threats. The program launched by the national cybersecurity alliance to educate SMEs on better protection strategies against cyber threats is an excellent example of the roles that operational partnerships play.
Popular Cybersecurity Alliances
Many leading IT companies like Airbus, Samsung, and Google (to mention a few) have come together to tackle cyber threats collectively. Major key alliances in the tech realm are;
1. Cyberthreat Alliance
Also known as CTA. It has been in existence since 2014 after an informal pact agreement between Fortinet, Palo Alto Networks, Symantec, and McAfee. It is mainly a sharing platform for member companies. The alliance boasts of adhering to five principles that govern its mannerisms. The laws are context rules, time is of the essence, radical transparency, for the greater good, and you must give to receive. The alliance is based on the value of trust, efficiency, and unity.
In CTA, the efficient and timely sharing of information is one of the constituents of its success over the years. In case of a new kind of malicious cyber threat, the information is shared promptly across the members to ensure they are aware and protected. It also gives a good chance for creating solutions to cyberthreats through the sharing of ideas or strategies. The alliance requires all members to share a minimal amount of intelligence to avoid the free-rider problem. This ensures all members are active and involved in the process. All members are treated with equity regardless of their position in the market. CTA focuses on defending the digital ecosystem.
2. Trusted Computing Group
First established in 1999 under the name Trusted computing performance alliance. The group was founded by Microsoft, Hewlett-Packard, Intel, IBM, and AMD. The alliance was announced in 2003 under its current title to succeed the prior alliance. Other companies have then joined. TCG ensures secure computing through the protection of user data across devices and storage. The group currently operates with a minimum of 100 members from all over the world. A trusted computing group offers a wide range of data security solutions to its members. Some of these services include; data storage device encryption alerts on malware and encryption of data transmittance. The alliance strongly emphasizes trust among its members.
3. Global Cyber Alliance (GCA)
The GCA is a robust international alliance formed by Sony, Adobe, Attivo Networks, Symantec, Juniper Networks, MasterCard CyberSecOn, Microsoft, Telos, Bloomberg, and Verizon. The group was formed mainly as a cross-sector effort to eradicate cyber risk and improve our connected world. The group’s mission is achieved through a qualitative assessment of the impact the alliance has on cyberspace. GCA focuses on uniting the global community across all geographical locations and sectors. The members enjoy freely available cybersecurity solutions provided by the alliance. Since its formation in 2015, GCA has seen an increase of members from the pioneering three organizations. Now there are over one hundred members.
4. The National Cyber Security Alliances (NCSA)
The alliance is a unique partnership between the federal government, educational organizations, trade associations, and leading private sector companies to provide a secure internet experience. In 2002, the group envisioned providing a safer digital experience as a recipe for; free flow of content, reliable and widely available connectivity, trustworthy commerce, and the creation of multiple communication platforms. NCSA is Governed by a very devoted and involved cadre of volunteer leaders from CISCO, Microsoft, RSA Security Inc, America online, and BellSouth Inc. Small businesses, institutions, and home users are the primary target audience of the alliance. Through the unique private-public partnership, the coalition focuses on promoting computer safety and ethical behavior online.
5. International Cyber Security Protection Alliance (ICSPA)
ICSPA is a not-for-profit organization that supports law enforcement units globally in their efforts against cybercrime. The alliance was formed to offer funding, expertise, and support to assist law enforcement agencies in handling malicious cyber activities, both in local and international markets. ICSPA membership includes national and multi-national corporations recognizing the importance of providing resources and other assistance to law enforcement departments in their fight against cybercrime.
Governments and institutions that understand the need to support other countries in the fight against cybercriminals support ICSPA. The alliance, in turn, channels the resources to beneficiaries to increase their knowledge, capabilities, skills, capacity, and expertise needed to reduce the impact of cyberthreat on businesses, customers, and citizens around the world.
6. International Alliance under NATO’s Cybersecurity Policy
Cybersecurity is an important topic of NATO’s summit agendas since the 2002 Prague summit, where Allied leaders acknowledged the need to defend against cyber threats. NATO’s purpose as a cyberspace alliance states, “We must be able to operate as effectively in cyberspace as we do in the air or land, and at sea to strengthen and support the Alliance’s overall deterrence and defense posture.”
In 2014, NATO released the first cyber defense policy for adoption and had continually upheld it with cyberspace’s recognition as a domain for military operations among the 28 member states. NATO’s purpose statement reveals that military activities can only be achieved through military means and cyber defense efforts. Over the years, the Alliance and its allies have placed technical and operational strides to mitigate cyber threats.
7. Other Cybersecurity Alliances
Other vendors in cyberspace partner with one another to enhance their protection against broader threat vectors and increase their capabilities in curbing cyber incidents at different phases. In this case, one party can be assigned prevention and detection while the other mitigates and recovers.
The Success of Cybersecurity Alliances
Digital technology’s success depends on broader connectivity. Therefore, when companies come together, they create a pooling of ideas and information on the current cyber threats. The companies are, consequently, left in a better position to evade or combat the ever-evolving cyber-attacks. So far, these alliances have proved to be beneficial. The president of France recently launched the “Paris Call for Trust and Security in Cyberspace,” This was one of the greatest mileages covered in terms of governments being pushed to invest in cyberspace security. This was a symbolic pledge by the state to improve international standards and cybersecurity practices. Sixty-three countries also joined the revolutionary move along with many other companies, civil and international society organizations.
Some factors, however, have been seen to derail the attainment of the full potential of cybersecurity alliances. Unhealthy competition among businesses and companies is a significant flaw in searching for reliable solutions to cyber threats. Some of the cyberattacks are orchestrated by competing companies to stall their competitors. This can also be a derailing factor if such a company is a member of an alliance, with access to the group’s information. As with any other venture, malpractices are numerous in the digital networking world. As companies come together to combat cyberspace risk, other companies fund the cyberattacks for their gain.
Governments have greatly influenced the slow pace of alliance success. Isolation retards the effort to address cybersecurity issues collectively. Digital separation is one of the worst forms of jeopardy to the cooperative efforts of cybersecurity alliances. State-funded hackers hide behind national firewalls to attack other governments and companies with malicious intent. This indicates the negative contribution of federal policies to the war against cybercrimes.
Do Companies with IT Security Departments Need to Join a Cybersecurity Alliance?
With the increase in cyber threat vulnerability, most IT companies have internal cybersecurity departments. These departments are solely meant to mitigate any possible cyber attacks that may be attempted on their company. These departments are single units with limited capabilities as compared to a comprehensive source of an alliance. Most of these companies are victims of the same cyber threats. It is, therefore, apparent that any of these cybersecurity departments would immensely benefit from a more significant source of solutions and information in regards to the cyberthreat. These departments’ work is to identify risk points and apply the best solutions and practices. Joining an alliance would help a company learn of possible risk points and have various solutions to choose from.
Cybersecurity alliances not only offer solutions to their members but also promote digital peace. Alliances seek assistance from the government, especially for companies under attack. Although they seem stable, these groups always ask for help from other agencies. While doing this, they ensure a calm digital ecosystem by upholding accountability and trust as core values. While every company does not need to join the alliances, it is still essential for most web-based companies to work collectively. If one company falls prey to a cyber-attack, the others will help find possible solutions to the attack. The alliances are based on symbiotic relationships where all parties are gaining. Apart from the victim companies, the other member companies would also benefit from gaining insight into combating a cyber threat in the event of an attack.
Joining an alliance would significantly improve the capabilities of the cybersecurity departments in companies. They would be more equipped with a broader scope of possible risk points and possible solutions for the risks. Hackers have well-established and organized communities where they cooperate to infiltrate other digital systems. Therefore, it makes perfect sense to combat these cyber threats in a collective organized manner. The scope of these cyber-attacks is everchanging.
Benefits of the Alliances to Organizational Cybersecurity
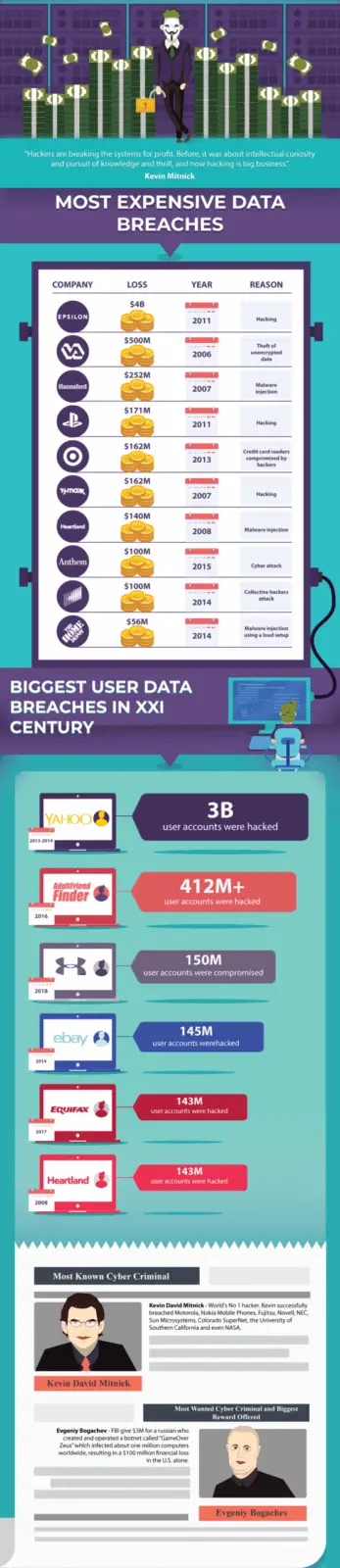
Cybersecurity has remained to be a key challenge for most organizations. Emerging IoT, 5G networks, and sophisticated cyber-physical systems have caused cybersecurity to be extremely complicated. If a data breach occurs, as was the case with Equifax, British Airways, and Facebook, trust existing between businesses and key policymakers might be affected. Hence, enterprises bridge this trust gap through cyber alliances, and more importantly, achieve better cyber defenses. As previously mentioned, normative and operational are the main types of cyber alliances. They both purpose to ensure the security of future digital networks and the internet.
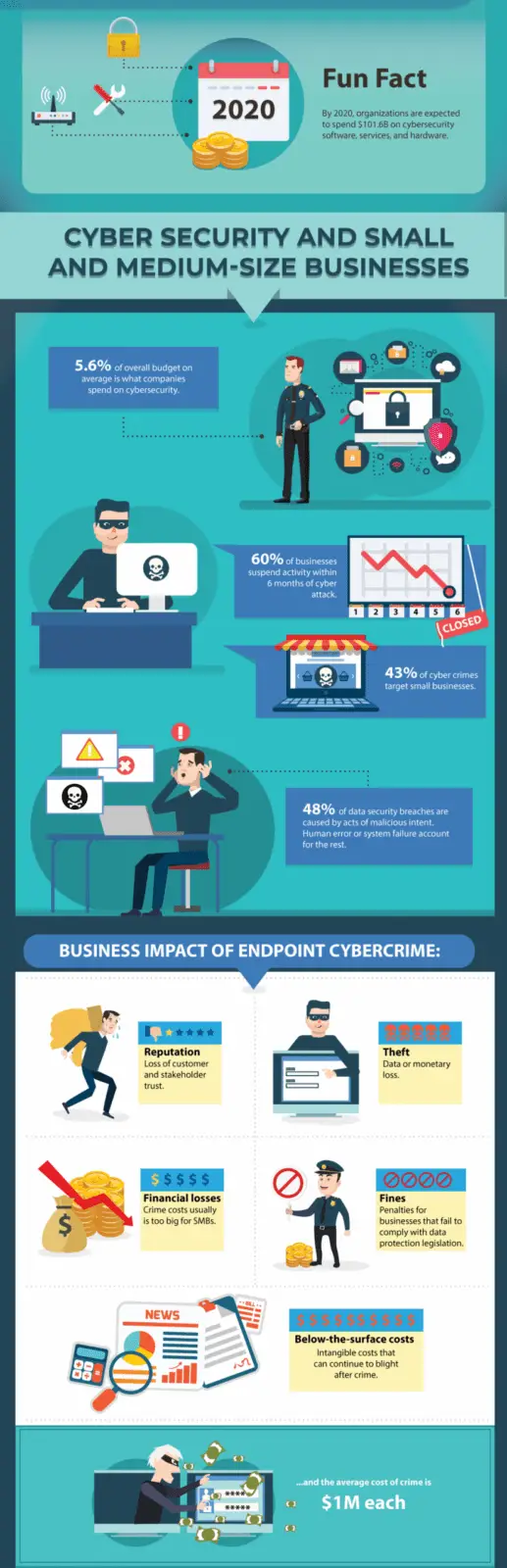
In this case, a business can opt for an operational alliance if it intends to enhance its cybersecurity posture. Small and medium-sized businesses with insufficient resources often find this option to be attractive. An operational alliance is also suitable for organizations seeking to structure new security-oriented practices. Since adversaries focus their campaigns on exploiting human users’ weaknesses, companies need to develop secure practices as far as network, system, or network access is concerned. Moreover, operational alliances enable organizations to share technical and intelligence data with other alliance members. The intelligence ensures they remain on top of all the latest cyber threats and measures for mitigating them.
Operational alliances are also ideal for companies with an established security or Chief Information Security Officer (CISO) department. Such departments handle data related to cybersecurity events and remain informed of the latest threats and appropriate actions for addressing them. One such example is the program by the National Cybersecurity Alliance. The program provides up-to-date information on how SMEs can use the best cybersecurity structures to protect themselves.