The threat of malware attacks in our digital world cannot be overstated. Shockingly, 94% of these attacks come from seemingly innocent emails.
Malign software, or malware, refers to a broad umbrella of malicious programs used by cyber attackers to breach secure networks and access sensitive data without authorization.
One notorious example that demonstrates the severity of malware attacks is the infamous WannaCry ransomware incident, which targeted countless victims worldwide and caused significant operational disruptions and financial losses.
Various techniques are deployed by these cyber adversaries to execute malware attacks. The most common among these methods is through deceptive emails, a tactic that is as ubiquitous as it is damaging.
Now, let’s clarify what ‘unauthorized access’ means. In simple terms, it refers to when an entity gains access to a network, system, or data without being granted the necessary permissions. Imagine a stranger entering your house without your knowledge or consent; that’s how malware sneaks into a computer system.
Importantly, it’s not all doom and gloom. There are various preventive measures we can take to safeguard against such attacks. Regularly updating software, installing reputable security programs, practicing caution when opening emails from unknown sources, and refraining from clicking on suspicious links can significantly reduce your risk of falling victim to malware.
While discussing these malicious attacks, it’s important to understand that there are different types of malware, each with its unique behavior and potential damage. These include viruses, worms, trojans, and more. Future sections will delve into more specifics of each type and their corresponding preventive measures.
Cybercriminals utilize cunning methods, such as social engineering, to deceive individuals into installing damaging software. Additionally, they employ command-and-control servers to direct advanced malware to carry out detrimental actions. This includes extracting sensitive data from an infected system remotely.
To better understand cybercriminals’ tactics, let’s delve into the kinds of malware attacks. Using social engineering, cybercriminals may lure their targets into various ambushes, including ransomware, adware, and botnets, among others. For instance, think about how an unsuspecting user could be tricked into installing what seems to be a legitimate app, only to find out later that it was ransomware. Another scenario could involve cybercriminals using social engineering to exploit their victim’s device for crypto-jacking. Real-life illustrations of these attack scenarios can clarify how dangerous these threats can be.
Apart from these, there are harmful payloads that these malware carry, for instance, the siphoning of sensitive data from an infected computer. Tying this back to the broader consequences, it isn’t just about the immediate loss of data. It could lead to loss of business opportunities, or worse, damage the company’s reputation. Thus, understanding these tactics gives us a glimpse of how critical network and data security are in our digital age.
The world of cyber threats is always morphing with new varieties of malware surfacing constantly. Given this scenario, it becomes critical to comprehend the attributes and peculiarities of different types of malware attacks to devise effective preventive strategies.
For instance, consider the pernicious types of malware like ransomware, adware, malvertising, backdoor attacks, Trojan horse, spyware, browser hijacker, keyloggers, bots, botnets, RAM scraper malware, crypto-jacking, and more. Each type has unique characteristics and impacts computer systems in distinct ways. Understanding these specifics is our first line of defense.
Preventing malware attacks isn’t just about understanding them, but also implicates on-going practical measures. Regular software updates can patch vulnerabilities that malware might exploit. Being savvy about potential threats such as suspicious emails or sketchy downloads is another crucial preventive step.
By equipping ourselves with ample knowledge and adopting these precautionary steps, we can signifcantly enhance our chances of thwarting malware attacks.
To delve deeper into this topic, feel free to explore other reputable sources for a more comprehensive understanding and comparison.
Let’s take a look at the most prominent malware exploits today.
These hostile programs, under the collective term “malware,” encompass viruses, worms, trojans, and more nefarious software that hackers employ to gain unauthorized access to data and systems.
For instance, imagine a well-known organization suddenly finding their systems compromised, their confidential data breached and their operations halted. This could be due to a particularly potent strain of ransomware, a type of malware that locks up a system until a ransom is paid. Learn more about ransomware here.
Another prevalent malware is adware. Imagine surfing the internet and your screen gets flooded with unwanted, distracting ads. This is the work of adware, a software that displays unwanted ads and can pose potential risks to your system and privacy. Read more about adware here.
Regardless of whether the malicious software is created by a lone wolf hacker or a state-sponsored entity, the damage inflicted to systems—be it a personal computer, a server, or an entire network—can be substantial.
Let’s delve deeper into the world of malware, understanding their impact and how they shape the cyberthreat landscape!
1. Ransomware Attacks

Ransomware is malicious software that encrypts essential information and denies users from accessing computer systems. Hackers use ransomware attacks to blackmail victims into paying a certain amount of money to get the decryption code. Generally, criminals demand ransom in cryptocurrencies. If victim delays or fails to pay, their sensitive information will be deleted or sold in dark web forums.
Ransomware attacks result in grave consequences for the affected victims, such as lost business opportunities, network and system downtime, loss of critical information, and destroyed reputation. Ransomware attacks are among the most common types of malware attacks. There were more than 304 million attacks recorded globally in 202. The average cost of a ransomware attack on a business Is $133,000. Security analysts indicate that in 2021, ransomware attacks against businesses occur every 11 seconds—the global cost associated with recovery exceeding $20 billion.
2. Types of Malware Attacks: Viruses

Computer viruses consist of malware designed to modify software programs by inserting malicious codes into an infected computer. Virus attacks usually use self-replication across a network. Successful virus replication results in higher infection rates in the computer system connected to the infected network.
Cybercriminals create computer viruses for various reasons. The top ones are sabotaging a network to deny essential services to an organization, monetary gains, and proving that a protected IT environment is hackable. Attackers leverage newer technologies to develop and execute more advanced computer virus attacks. Statistics show that at least 6,000 new viruses are created each month.
3. Adware Attacks

Adware attacks are a form of malware attacks that put constant advertisements on the web browser of an infected computer. These programs are often harmless since a perpetrator intends to advertise services or products without a victim’s consent.
Based on their nature, adware attacks can be highly annoying since they pop up at any time when a user is accessing internet services. Adware attacks typically distinguish themselves as legitimate programs or piggyback on other running programs to trick users into clicking and installing them. Adware attacks remain to be highly profitable since they generate revenue automatically once a user clicks them. In 2020, some 1,841,164 people were victims of adware attacks.
4. Malvertising
Almost every internet user has encountered the following message or something similar when accessing the internet; ‘Your device is running low on memory because of malware infection. Click here now to clean it using antivirus’. However, clicking the advertising banners usually downloads malware or links to a malware-infested website. Malvertising attacks resemble adware attacks.
Malvertising, short for malicious advertising, is an attack method where harmful cyber actors inject malware-loaded advertisements into different advertising websites or networks. Hackers create ads to resemble actual advertising to attract more users and leverage the opportunity to spread malware.
In the second quarter of 2020, malvertising threats remained 72% higher than the normal average as malicious cyber actors exploited opportunities resulting from the COVID-19 pandemic.
5. Types of Malware Attacks: Backdoor Attacks

A backdoor attack is a concealed technique that bypasses deployed encryption or authentication schemes in a network, embedded device, computer, or other digital products.
Attackers execute backdoor attacks by planting malware, such as a trojan horse, in a remote part of a running software program or using a separate malicious program disguised as legitimate software.
Also, backdoor attacks occur when cybercriminals inject malicious code into a device’s operating systems or firmware to monitor all activities done on the device. The attacks enable perpetrators to access encrypted sensitive data or files or gain secure, remote access to a computer or network.
The European Network and Information Security Agency (ENISA) identifies backdoor attacks as one of the primary cybersecurity incidents affecting businesses within the EU and globally.
6. Trojan Horse

Trojan horse malware programs are developed based on the ancient Greek story where a wooden horse was used to hide soldiers entering Troy. Similarly, a trojan horse malware deceives victims that the malware is legitimate software while concealing a harmful program. For example, attackers can target several individuals with email attachments containing what appears to be genuine software. However, opening the attachment installs a trojan automatically.
Trojan horse malware attacks are dangerous since the payload can execute other attacks. Typical uses of trojan horse attacks include creating a backdoor to provide hackers unauthorized access to infected machines, personal information, online banking details, or to carry out ransomware attacks.
7. Spyware Attacks

A common type of malware is Spyware. Spyware collects and exfiltrates information from a person’s or an organization’s network and operating systems without the knowledge or consent of the victims.
It is simply a harmful program that attackers deploy to spy on all activities done on a computer or mobile device. The primary essence is gathering and sending sensitive information, such as credit card details, passwords to accounts holding sensitive data, online bank account data, and personally identifiable data, for use in malicious events.
Most spyware programs spy on a user’s activities. Some contain additional capabilities, including installing additional software programs and changing the security settings on a device.
A 2021 report indicates a 79% increase in business malware detections resulting from increased use of spyware and other modes of malware.
8. Types of Malware Attacks: Browser Hijacker

Cybercriminals use browser hijacker malware, popularly referred to as browser redirect virus, to make unauthorized modifications of a computer web browser settings or configurations without the user’s consent.
Browser hijacker malware enables adversaries to redirect web users to websites, often malicious ones, involuntarily.
The malware attack results in various adverse consequences, including installing multiple toolbars on the hijacked browser, the generation of numerous malvertising or adware pop-up alerts, web pages loading slower than expected, and changing the default search engine to one under the hackers’ control.
Browser hijacking attacks are financially motivated, as attackers use the tactic to generate revenue through adware and malvertising or to install spyware programs to monitor a user’s web browsing habits and activities.
Malwarebytes regards browser hijacker malware to be among the top ten malware attacks targeting businesses today.
9. Keyloggers

Keyloggers, also known as system monitoring or keystroke loggers, are malware types created to monitor and record all the keystrokes on an infected computer’s keyboard. Other types of keyloggers work on mobile devices running different types of operating systems.
A keylogger malware program stores the collected information and sends it remotely to a malicious cyber actor who can then use other tools to extract sensitive information. In comparison to most malware attacks, keyloggers don’t harm the systems they infect but instead facilitate unauthorized access to confidential data. Attackers often use keyloggers to collect sensitive financial and personal information and use it for monetary gains.
10. Bots and Botnets

A bot is any device injected with malicious codes under the control of an adversary and used to execute harmful functions. A collection of numerous bots forms a network of harmful bots referred to as a botnet. Botnets may comprise a collection of Internet of Things (IoT) devices, mobile devices, servers, or personal computers.
Threat actors control botnets remotely, and all their operations are undetectable to a computer user. The most common attacks executed using botnets include DDoS attacks, click fraud campaigns, and sending spam or phishing emails.
Bot and botnet attacks are pervasive, with more than 1.3 billion bot attacks detected in the third quarter of 2020.
11. RAM Scraper Malware Attacks
RAM scraper attacks are malware attacks that assist cyber adversaries in finding and stealing personal information. It is a malware type that captures sensitive information from a volatile random access memory.
Modern RAM scraper malware is designed to inject itself into a running process or execute directly on a computer. This allows it to evade detection. Once the malware infects a system, it can be used to read and exfiltrate social security numbers, credit card data, encryption keys, and passwords. RAM scraper attacks can hide the read information in a local storage option or send it to the attackers remotely.
The malware mainly targets businesses since it makes it to the top four malware families targeting points of sale (POS).
12. Crypto-Jacking

Since bitcoin and other cryptocurrencies are experiencing a rapidly rising value, cybercriminals deploy crypto-jacking malware to mine cryptocurrencies using unsuspecting victims’ machines and resources.
The crypto-jacking malware utilizes JavaScript of a victim’s web browser to mine cryptos without the permission or knowledge of the end-user. Essentially, a malicious individual steals the memory, CPU time, power consumption, and other resources.
The more attackers run crypto-jacking malware on the JavaScript, the more the computing power expands. As such, it is crucial to note that crypto-jacking malware is not necessarily harmful but causes the infected machine to run much slower.
A threat landscape report by Symantec shows a 163% increase of crypto-jacking malware in quarter two of 2020.
13. Rootkits
Rootkits consist of malware programs developed to provide attackers with unauthorized access to a software or computer network. A rootkit is designed to mask its presence or other computer programs that make up the rootkit.
Cybercriminals employ various tactics to install and deploy a rootkit, including an automated installation if a user clicks it or direct attacks, such as phishing, vulnerability exploitation, and brute-force attacks, to enable the attackers to install it using administrator access. Also, rootkits can subvert antivirus software to prevent it from detecting malicious programs or activities. As such, they are hard to detect.
Such capabilities make rootkits even harder to remove, especially if they embed themselves in a hardware’s firmware. Rootkit attacks may necessitate the complete replacement of the infected device.
14. Types of Malware Attacks: Crimeware

Essentially, crimeware is any malicious computer program or set of harmful software developed for the sole purpose of facilitating illegal activities in an online environment. Most browser hijackers, keyloggers, and spyware malware programs fall under the crimeware category.
In particular, an exploit kit, a collection of various tools put together, assists cybercriminals with minimal technical skills to execute an attack. Exploit kits, and other sets of crimeware tools, are readily available on dark websites for an affordable cost.
A Verizon report places crimeware among the top three cybercrimes in 2019 that accounted for at least 93% of attacks and breaches.
15. Hybrid Malware Attacks
Hybrid malware attacks are a modern combination of existing malware attacks, such as ransomware, viruses, trojan horses, and worms. Also, hybrid malware comprises the characteristics of all the incorporated malware programs. As such, hybrid malware is capable of executing multiple attacks simultaneously. For example, a hybrid malware combining the characteristics of a worm and virus can utilize the virus’s characteristics to alter the code of a legitimate program, and at the same time, use the worm’s ability to propagate across a network and reside in a computer’s memory. Therefore, these forms of attack payloads are significant and devastating since multiple malware programs execute simultaneously.
16. Computer Worm Attack

Computer worms are malware programs created to infect a computer or network and self-propagate to infect other connected devices while remaining active on the infected machines. Worms exploit the security failures and vulnerabilities present in the targeted networks before spreading while replicating to all connected devices.
The implication is that a worm attack does not depend on any user actions, such as clicking or installing a malicious program, in spreading and executing, since they propagate automatically if any device is infected. However, in contrast to virus malware attacks, worms may not cause actual harm but may result in increased bandwidth consumption, potentially disrupting network activities and critical IT infrastructure.
17. Drive-By Attacks
A drive-by attack is not a malware attack but rather a method used to distribute different types of malware. Hackers use the method to inject malicious scripts into the HTTP or PHP code used to create a vulnerable website. The approach requires attackers to design the malicious scripts to install malware automatically anytime an individual visits the insecure website, hence the term drive-by attack. Moreover, the adversaries can design malicious scripts to redirect a user to a malware-infested website automatically.
Malware attacks executed using drive-by attacks exploit vulnerabilities present in software installed on a host system, operating system, or web browser. Microsoft recently warned of new drive-by attack methods that target Firefox, Chrome, and Edge users.
18. Fileless Malware Attacks
Fileless malware attacks occur when attackers leverage already installed software programs to execute a malicious attack. In contrast to most malware attacks, a fileless malware threat uses existing applications that are already considered safe. As such, this type of malware does not require a malicious program to execute an attack.
Fileless malware usually exists in a computer’s RAM. It typically accesses default operating system tools, such as Windows Management Instrumentation and PowerShell, to inject the malicious code. Since they are trusted applications that execute system tasks in multiple endpoints, they are prime targets for attackers performing fileless attacks. Fileless malware attacks are among the fastest-growing types of attacks since they registered a 900% growth rate in 2020.
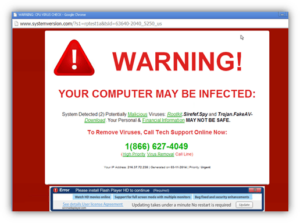
19. Types of Malware Attacks: Rogue Software Programs
Cybercriminals create pop-up windows and alerts that look legitimate, advising users to download security software, update their current systems, or agree to terms to stay protected. Rogue programs trick users into clicking them by displaying alarming messages. For example, the program may trick users into believing that it is an antivirus product that removes all types of malware. Rogue security software is also known as fraudware, rogue scanner, or rogue antivirus. Real-world examples of rogue software include Antivirus Plus, Spy Sheriff, Total Secure 20XX, AdwarePunisher, Registry Cleaner, and WinAntivirus.
However, rogue software programs are malware. It is a common threat targeting desktop computing. The most used infection vectors are spam campaigns, black hat SEO, and malvertising.
20. Harmful Mobile Applications

Hackers usually reverse-engineer legitimate mobile applications to attract innocent users into installing them. The essence of reverse engineering legitimate application is to attract potential victims. For instance, malicious cyber actors can reverse-engineer premium applications and upload them as a fully paid-for app.
Many users who prefer using cracked apps may install malicious applications introducing malware in their mobile devices. Malicious mobile applications enable attackers to exfiltrate sensitive information, extort users through blackmail, and gain unauthorized access to secured networks.
21. Grayware Attacks
Grayware attacks involve the use of unwanted applications to annoy computer users. Instead of harming the infected computer, grayware programs may cause a system to behave anomaly through events, such as high computing resource usage and lagging.
The term grayware was coined to indicate a thin line between legitimate software programs and virus applications. While grayware may not be harmful, it is vital to detect and remove it immediately to prevent unwanted system behavior or downtime. Examples of grayware include adware and spyware.
22. Exploit Kits
Exploit kits assist hackers in exploiting existing vulnerabilities in an application or computer software program. Exploiting the security flaws provides entry points for inserting various forms of malware in a targeted system. Exploit kits contain unique codes that can deliver malware payloads, identify vulnerabilities, and cause harm. They are common methods of executing malware attacks. Cybercriminals can quickly deploy them on a victim’s computer using drive-by attacks.
23. Logic Bomb

A logic bomb is also known as slag code. It consists of malicious code appended to a software program. It is triggered to execute after a given occurrence, including logical conditions, time, or date.
Logic bomb facilitates supply-chain attacks since the malware is set to ‘explode’ after meeting certain conditions. This means it is undetectable until it is too late to stop the attack.
Logic bombs cause variating levels of destruction. Attackers have infinite sets of conditions to choose from when appending the malicious code. Logic bomb attacks may lead to impacts, such as hard-drive cleaning, file deletion, and sensitive data corruption.
24. Types of Malware Attacks: Droppers
Droppers are computer programs that hackers use to install all types of malware. A dropper is usually free of malicious codes and, therefore, undetectable to antivirus products. Droppers can install a malicious application once it is deployed on the targeted system. It can also download new malware or updates to an already installed malicious software.
25. Polymorphic Engines
A polymorphic engine is commonly called a mutation or mutating engine. It is software capable of transforming an application into another version with different code but provides the same functions. Hackers use polymorphic engines on malware types like viruses and shellcodes to conceal them from antivirus or antimalware scanners.
26. Scareware
Scareware malware is a type of malware that manipulates users. It tricks users into downloading or purchasing unwanted harmful programs out of anxiety, perception of possible threats, or shock.
It is categorized in the same class as other types of malware, including ransomware, rogue security applications, and scam software. These trick or threatens victims that they will be harmed unless they use it. In most cases, the recommended software turns out to be malware.


