Hackers do not discriminate between big or small enterprises, which is a reason that answers the question, why is cybercrime expanding rapidly. The rise of data breaches, ransomware attacks, and cyberterrorism incidents is unprecedented. Recent publications of high-profile attacks are a testament that adversaries are unrelenting in their malicious intentions. For example, malware variants, such as ZCryptor, Petya, and WannaCry, have caused untold reputational and financial damage to organizations all over the world.
As cybercriminals leverage emerging technologies to advance their malicious campaigns, companies are increasingly exposed to cybersecurity threats. Moreover, digital innovations are being applied in critical sectors on a large scale. In turn, hackers have exploited digital technologies’ opportunities to gain high payoffs from the proceeds of cybercrime. The rapid expansion of cybercrime requires organizations to implement stringent precautions to eradicate vulnerabilities that can cause attacks. Various reasons have led to the rapid increase of global cybercrime.
Common Types of Cybercrime
Cybercrime consists of all activities that use or target a networked device, computer network, or any I.T. infrastructure. Cybercriminals use computer technologies to commit illegal actions, such as stealing user identities, violating personal privacy, or trafficking in intellectual property and child pornography. They exploit security weaknesses in digital systems to attack information assets via the Internet.
The following are some of the most popular types of cybercrime:
1. Identity theft
Identity theft is a scam practice where criminals use the identification credentials of another person for malicious reasons. For example, hackers may gain unauthorized access to a person’s banking account or credit card information and use it to steal funds or make purchases using the owner’s identity.
Although the identity theft concept has been around even before the Internet advancements, the increased use of digital information makes it easier for adversaries to steal a victim’s identity. Identity theft crimes are prevalent in various online deals and often come in forms like ad pop-ups, spam emails, and phishing attacks.
2. Phishing scams
Cybercriminals use phishing attacks to trick victims into revealing sensitive information, such as passwords, bank account information, social security number, and other personal information types. Phishing scams have proved to be highly effective since criminals require minimal resources to execute the attacks.
Hackers can create a phishing website, which mimics a real website to trick users into providing sensitive information. Criminals may also send email messages in bulk containing links to malicious websites or attachments, hoping that users will click them.
3. Malware attacks
Malicious cyber actors use malware attacks to infect a computer network or system with viruses, trojans, ransomware, and spyware. Malware is any program developed to harm a computer. A malware infection can enable cybercriminals to compromise an organization and steal highly confidential information, such as intellectual property and competition strategies.
One of the most popular types of malware is ransomware. This attack enables a cybercriminal to lock a victim’s computer systems and only provides a decryption key after paying a ransom. An example of a ransomware attack is the global WannaCry attack. Cybercriminals infected thousands of computer systems across the world.
4. Distributed Denial of Service (DDoS) attacks
Cyber adversaries use DDoS attacks to take down organizational networks and computer systems. Hackers target a company with an overwhelming amount of network traffic to prevent authorized users from accessing or using the network resources. DDoS cybercrimes overwhelm a computer system using standard communication protocols for spamming the system with numerous connection requests.
Cybercriminals often deploy the strategy in cyber-extortion schemes, threatening a DDoS attack unless they are paid a certain amount of money. Malicious actors may also use DDoS tactics as a distraction while they commit other types of cybercrimes. A recent example is the 2017 DDoS attack that impacted the U.K. National Lottery Website. The unavailability of the lottery’s mobile application and website prevented online users from playing.
Recent Cybercrime Statistics
There has been an unprecedented increase in cybercrime threats in recent years. Despite this, many people and organizations fail to take cybersecurity seriously, with individuals using common credentials to secure their accounts and devices while others use devices with inadequate security.
The following cybercrime statistics indicate the severity of the cybercrime threat:
1. There is an attack every 39 seconds: A University of Maryland study revealed a computer attack occurs every 39 seconds. The adversarial incident could be in the form of a phishing attack, malware attack, or direct hacking.
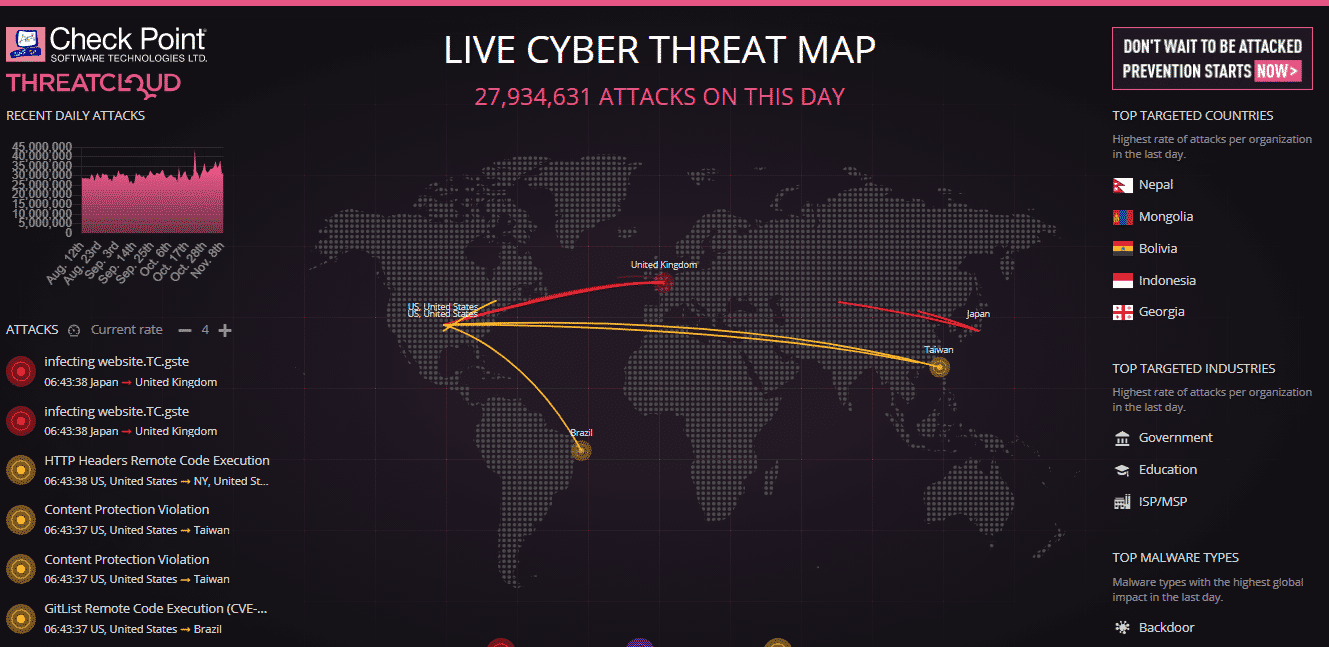
Screenshot: A live threat map showing more than 27 million attacks have occurred in a single day (Source: Check Point Software Technologies)
2. 78% of U.S. organizations have been victims of attacks: Most hackers target companies that process personal or financial information due to monetary gains. Financial motivation is among the reasons why cybercrime is expanding rapidly. Cybercriminals usually go for small- and medium-sized enterprises. They often lack the resources to implement robust cybersecurity measures. Such businesses are the majority and, therefore, form the majority of the victims.
3. There has been a 54% increase in mobile malware variants: The increase of mobile malware indicates how cybercriminals have continually enhanced their attack techniques. An increase in the usage of mobile and IoT technologies has seen malicious adversaries develop newer sophisticated malware variants.
4. 63% of businesses have been victims of data breaches: A Dell survey found that the data of 63% of companies were compromised due to a software or hardware-level security breach. The same survey indicated that only 28% of organizations are satisfied with vendor-implemented security measures.
5. There was a 14% increase in unique malware programs: According to Kaspersky, its web antivirus solution detected 24,610,126 unique malware programs in 2019, a 14% increase from 2018. The sharp rise of malware advancements subjected almost 20% of internet users to various malware attacks.
Why is cybercrime expanding rapidly? The 6 reasons
1. An unprecedented rise of cyber-stuff
The prefix cyber has become common in virtually all crimes involving digital technologies. We have become accustomed to words like cyberwar, cybercriminals, and cybercrime. Therefore, it is vital to stop perceiving cyber-related attacks as sophisticated concepts and instead think of them as crimes hackers commit through easy tactics.
Today, it is much easier to steal personal information or compromise the security of a company remotely. Numerous automation tools with A.I. and ML capabilities have advanced, enabling criminals to commit cybercrimes without the need for high skills or technical expertise. The tools are readily available on the dark web for a small amount of money. Anyone with trivial technical inkling can easily find and use them. As a result, there have been higher levels of cybercrime compared to yesteryear.
2. The Internet architecture
The Internet infrastructure’s original architects focused more on durability and stability and gave little thought to security. They were not security-conscious when designing and building network infrastructure. Besides, the architects never thought that the Internet would provide a platform for transmitting millions of dollars or information worth a lot more than it is today.
As the Internet advanced to become more of a social and commercial space than for academic purposes, measures to make it more secure continue to be developed. Nevertheless, most of the underlying design depends on insecure transportation methods that can be hijacked with ease.
Cybercriminals have continued to exploit the security shortcomings to carry on their malicious campaigns. The Internet has also become central to most vital processes, including controlling critical assets and infrastructures. Hackers continue to capitalize on the Internet’sInternet’s insecurity to rump up attacks, resulting in the continued rise of cybercrime.
3. The role of hackers in information security
Most people today are paid to be professional hackers, professionally known as security researchers or ethical hackers. Their roles include enumerating security vulnerabilities in information systems and creating tools for demonstrating and detecting the flaws. The researchers then release the tools to the general public, most of which end up in malicious individuals’ hands.
Many cyber criminals use legitimate hacking tools to compromise systems and steal sensitive information. Also, other black hat hackers develop similar tools to facilitate the expansion of cybercrime activities. Since hackers have become more experienced and continuously gain access to newer technologies, there has been an explosion of hacking tools. Therefore, the cyberspace and information security field has become a race between the adoption of protective technologies and advancements of hacking tools and processes. The result is a rising wave of cybercrime.
4. Companies are slower in adopting strong security.
The reality of the current cybercrime landscape is that most companies don’t deem it profitable to overhaul their security systems unless the need arises. Profit-minded organizations usually hold off redesigning their security systems until they suffer an attack or their customers demand better security. A prime example is where Facebook failed to implement secure sessions until its CEO, Mark Zuckerberg’s account was hacked. Facebook only took user security seriously once the company deemed it as a personal problem.
Many other companies have the same security approach. Some may be aware that their systems or networks are insecure or vulnerable but fail to remedy time issues. Furthermore, most private and public entities have poor security practices, which further contributes to the continued rise of cybercrime.
5. Targeting people
For the longest time, humans have been the weakest link in the cybersecurity chain. Many computer users and company employees are untrained on the best security practices and secure system usage. While numerous users focus on security and software tools to detect and eliminate malware, cybercriminals have channeled their efforts on humans.
Most of the successful attacks begin by tricking unsuspecting victims into clicking on malware-laden attachments and websites. Cyber adversaries are adept at exploiting human trust through social engineering methods and other similar scams. Tricking users to volunteer information, such as passwords, banking details, healthcare information, and personal data, has caused cybercrime to rise significantly.
6. Internet of Things (IoT) proliferation
The current global IoT market is valued at $82.4 billion and is estimated to register a compounded annual growth rate of 21.3% between 2020 and 2028. IoT comprises devices that can connect to the internet. Each IoT device represents an attack surface, and the high usage of IoT systems has contributed to the rise of cybercrime.
Many businesses permit employees to use IoT devices since they are known to enhance productivity and streamline crucial operations. With so many endpoints introduced to a network, hackers can easily detect a vulnerable device and exploit it to commit a cybercrime. Besides, IoT systems are increasingly being used to control critical infrastructure and factory operations, thus attracting more adversaries. Vendors are also racing to release the most products due to the large market. The rush to outdo competitors causes manufacturers to include security as an afterthought, resulting in devices with exploitable vulnerabilities.
How can businesses protect themselves?
Since cybercrime is expanding rapidly, businesses should take proactive measures to protect themselves. The following recommendations can help in reducing cybercrime levels:
- Regularly update software: Updating software and operating systems regularly deny cybercriminals the opportunity to exploit vulnerabilities. Patching security flaws make one a less likely target, which is essential to lowering cybercrime.
- Outsource security services: Outsourcing security is the best strategy for small- and medium-sized businesses that lack the resources to strengthen their cybersecurity posture. Managed service providers have access to the latest and most effective security practices, tools, and professionals. Outsourcing security reduces cybercrime significantly.
- Protect against identity theft: Using VPNs in a home or corporate network can help prevent identity theft. It is essential to securely share personal information and passwords to prevent cybercriminals from intercepting the communication.
- Normalize training: Cybersecurity training and awareness should be a common occurrence for businesses and individual computer users. Being conversant with the best security
- Use robust antivirus/antimalware tools: Antivirus software programs enhance cybersecurity since they detect and eliminate harmful programs. Users must ensure to update the antimalware solutions regularly to gain access to the latest threat definitions.


