Over the last half a decade, Cyber-attacks has been considered as one of the biggest threat to the financial institution. Cyber criminal’s skill and techniques have evolved with technology; they have become more organized forming groups like Lazurus making it difficult for financial services to have the upper hand in the war on cybercrime. The loss from cybercrime is substantial in the banking sector raging from litigations, to cost of preventing another breach and a dent to the reputation of the institution.
Financial service providers such as the banking sector are more likely to be targeted compared to any other financial service sector.
Cybersecurity measures of banking sectors which adopt mobile and web to deliver services tend to have a weak security system that why many cybercriminals prefer to target online and mobile banking system. Besides, Cyber attacker manages to hijack customer and employees information detail and use them to penetrate the security system of the bank under cover of the dark web to steal bank data and money.
Let’s look at the various cybersecurity threat facing the banking sector:
Identity theft
Every year it is estimated that the banking sector suffers a loss of over $ 10 million through identity theft. According to the research by Javelin Strategy and Research, over 15 million Customer in the United States of America have fallen victim to this kind of fraud.
Identity theft is the use of persons and credit information without his or her consent to borrow money and conduct a purchase. When a data breach occurs, the data of the customers are either sold or bought in dark web by other cybercriminals to use in other violations of the customer account or financial sector.
Threat from employees
Human error and disgruntled employees contribute to a large percentage of the risk.
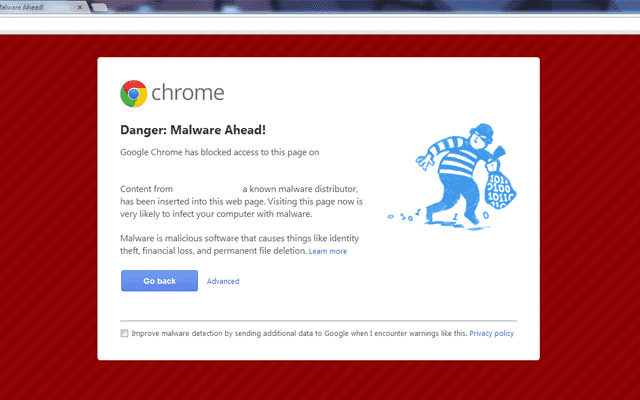
Many employees use their device to access the bank service or use the bank device to check their email. This creates an opportunity for malware and phishing attacks sent to them disguised as a genuine offer or gift. Additional, bank employee s who are unhappy about treatment by the institution steal sensitive bank information which they can decide to sell the information to cybercriminals.
Supply chain attack
In most network their security vulnerabilities which can easily be accessed by backdoor malware attack such as DNS lookup and connect following techniques which grant remote access to the attacker without even the user being aware. The hacker can bypass the detection system once he has access to the network.
One of the most significant supply chain attacks was in shadow pad where someone was able to find a backdoor in it genuine software hence exposing client’s information for exploitation.
The financial sector remains one of the biggest causalities of this attack.
Ransomware, it’s a software that is malicious in nature that holds captive the service of the victim until the ransom money is given out. Employees are prone to this attack when they open a link in a suspicious email which activates the malicious software into the system.
ATM malware and Jackpotting
Jackpotting case has been rampant in Europe and the USA. Criminal take advantage of the weakness in the software and physical state of the ATM; this allows the thief mostly dress in company service uniform to access the cash available in the machine reserves through a key that cracks the ATM. Furthermore, the money taken cannot be detected early; for it does not belong to any account; this allows the thief to able to escape without being noticed. Sometimes they leave skimmers; this is a device that scan people’s details such account information the information are sold off.
Synthetic fraud
This involves the creation of fake identity, from social security number to identification number. The attacker creates not just one but several, afterward they use them to seek credit from banks which they use to purchase goods and services. This social security number cannot be traced in the system or anywhere else because they do not exist. It is estimated that there is outstanding credit of more than $300 million which the people who borrowed the debt do not exist; this is according to research in wall street journal.