How does the PMP exam compare to the CISSP exam?
When someone asked me that question, I thought it was rather odd. How can you compare the PMP to the CISSP? These are two completely different tests on two completely different subjects. The PMP exam covers project management while the CISSP exam covers cybersecurity.
But then I thought about it.
The question is valid. I expect that many people may be considering both the PMP and the CISSP. Both of these certifications are considered the top certification in their respective fields. So, this question deserves some thought.
The value of the PMP vs. the CISSP.
The current number of people who hold the PMI PMP certification worldwide is 791,448. On the other hand, the number of people who hold the IS2 CISSP certification worldwide is 122,289.
So, there are far more PMPs in the world then there are CISSPs. In other words, holding a CISSP certification is much rarer than a PMP.
The first PMP exam was in 1984. The first CISSP exam was in 1994. So, the PMP has a 10-year head start. But this does not matter if you are comparing sheer numbers. Based on the numbers, it is harder to find CISSPs.
When I am deciding what certification to pursue, I want to know how valuable the certification is in the job market. The quickest way for me to test this is to search for the certification on Indeed.com. The results of the search will show the number of positions that either require or desire the applicant to have that certification.
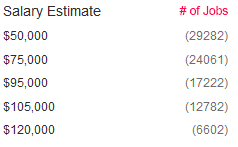
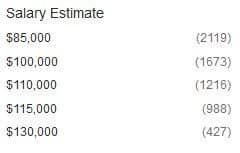
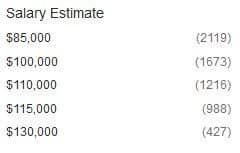
When I search for PMP in the Washington DC metro area, I find 2525 results. Here is a breakdown of the estimate salaries for these results:
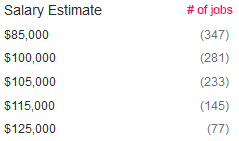
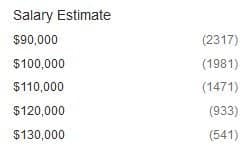
If I do the same search for CISSP in the same area, I find that there are 2707 results. Here is a breakdown of the estimated salaries for these results:
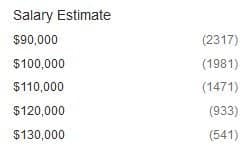
So, there are slightly fewer jobs available that require the CISSP certification. But the CISSP positions have a bit of a higher starting salary than the PMP.
So, I believe that the CISSP exam has more value than the PMP certification. But, the difference is not drastic, and both certifications are desirable for employers.
The Exams
Both the PMP exam is 4 hours. The CISSP exam does not have a set duration. Unlike the PMP exam, the CISSP exam is adaptive. This means that if you get a question correct, then the next question is a bit harder and so on. The CISSP exam ends when you meet the criteria of passing it or if the computer algorithm determines that you will not pass.
Therefore, there is no set time for the CISSP exam. Some people finish it rather quickly (I did). I was only presented with about 110 questions. Other people keep getting question after question and need to complete up to 150 questions. The questions are mind-bending and can take many minutes to answer each one. So an additional 40 questions can equate to a couple more hours of exam taking.
The PMP consists of 200 multiple-choice questions. These questions tend to have more than one “right answer.” This makes it tricky because you have to choose the answer that is “more correct.”
For this reason, when I got to a question that required a formula is was relieved. As long as I could remember how to do the math could be sure that my answer was correct. The non-formula questions were much more challenging. I had to debate on which solution was better and why. On many of the questions, I had to make a “best guess.” It is hard to maintain confidence when you are forced to make choices that you are not sure of.
The CISSP also consists of multiple-choice questions. Just like on the PMP exam, many questions do not have a clear, correct answer. And just like the PPM exam, I found myself choosing between 2 answers that I thought were both correct.
With the CISSP, the golden rule is that the least expensive answer is the best one. For example, if you are asked for the best way to mitigate risk, you should choose the answer that does the job a the least cost.
Which test is harder?
Both the PMP exam and the CISSP exam are challenging. Pass rates are not published for either exam, but it is said that less than 50% of people pass the CISSP exam on the first try. The numbers are said to be similar for the PMP exam.
But for me, the CISSP exam was significantly more difficult than the PMP exam.
I took almost the full four hours on the PMP exam. I spent a lot of time reviewing my answers, and there were only about six questions that I was completely unsure of. The PMP exam allows you to go back, review, and change answers. When you are complete with your review, you can click a button to end the test and see if you passed. By the time I clicked the complete button, I was pretty confident that I passed.
I said a prayer, and I clicked.
I believe that the testing software gives an intentional delay to keep you in suspense. After what seems like forever, the test results are shown.
Boom – I passed.
On the other hand, the CISSP exam is administered entirely differently. I mentioned before that the test is adaptive. If you get an answer right, the next question is more complicated. You get to a point in the testing where the questions become so obscure that no one can know all of the answers.
And you can’t go back and review or change answers on the CISSP exam. When you answer the question, it moves to the next one, and there is no looking back. Also, the test can end anytime. You don’t know when it will end or if the questions will keep coming.
I was on question 107, and I had a feeling that if I got the next one right, I would pass. For some reason, I also thought that if I missed the question, I would be going down in flames.
I answered question 107, and the test did not end.
Question 108 was on a topic that was completely unfamiliar to me. I analyzed the question and the answers and somehow became very confident that I was correct. The test continued until 110.
Then the test ended. There was no notification that I had passed or failed.
I left the computer and walked out. Biometrics were scanned again to ensure that I did not somehow change places with a smarter version of me.
I discouragingly walked out to the front desk, where the woman at the desk was looking at a computer. She printed a sheet of paper and folded it in half. She handed the paper to me, and I slowly opened it.
I was unable to decipher what the paper said because my mind did not yet recover from the exam. “Congratulations,” the woman said with a smile.
Boom again. I passed.
When people ask me which test was harder, I say that the CISSP was much harder than the PMP.