When Hackers Kill
Hackers have already – perhaps many times- have contributed to death by hacking into secure systems and releasing information. This information has lead to the loss of life in many different ways, including suicide and murder.
But hacking has now evolved to the point that cybercriminals can use computers to negatively affect and damage the physical world, including the murder of individuals and groups.
Hackers have the power of mass-murder in their hands right now.
Using malware to affect the physical environment is nothing new. One of the most famous cases is the Stuxnet virus that was used to destroy Iran’s nuclear centrifuges. This virus made the centrifuges spin out of control and took down 20% of Iran’s nuclear centrifuges.
Since the Stuxnet example, there have been many more hackers using computers to cause physical damage to steel mills, water dams, power grids, etc.
I can cite no cases where hackers have used the digital world to directly affect the physical world to cause the murder of a person. But that does not mean that it has not happened. Hackers have likely been able to pull off murder without being caught.
The number of ways that hackers can murder is staggering. There are thousands of systems that hackers could infiltrate to cause death directly.
The Airplane Hack
Pilots rely on computerized systems on planes to such an extent that newer planes can virtually take off, fly, and land by themselves.
Hackers can cause havoc on an airplane. The systems that control the plane have vulnerabilities. Cybersecurity experts agree that no system in the world is perfect. All systems have either major or minor vulnerabilities that are exploitable.
The pilot is the last line of defense against hackers. But people are also a week link when it comes to security. Hackers can use the pilot’s weaknesses to achieve their evil goals. The hacker could take control of instrumentation and provide false readings that would influence the pilot to make decisions that would lead to a plane crash. The combination of social engineering and airplane hacking would be a powerful and potentially deadly attack.
Zombie Automobile Attacks
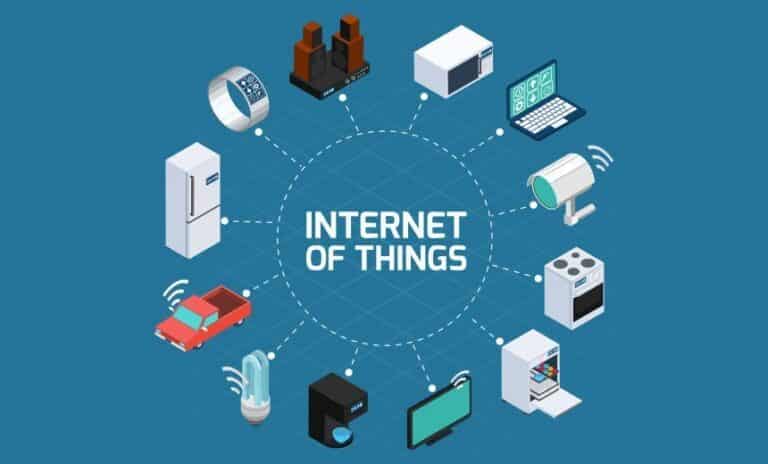
You can go to YouTube to see demonstrations of hackers unlocking Teslas remotely. Beyond that, hackers can take control of navigation systems and autopilot systems. Recently it was demonstrated that a car’s GPS could be hacked to make the driver drive to the destination that the hacker chooses.
As more and more cars increase their connectivity, there will be additional threats. Self-driving vehicles will be able to communicate with each other and have complete data on the driving environment.
Hackers have demonstrated that they can take over a car’s braking system, control the dashboard instruments, and start or kill the engine.
Many cars are implementing safety features such as “assisted steering” designed to steer the vehicle to avoid accidents. Of course, self-driving cars have systems that are in complete control. This means that a hacker can remotely take over a car’s steering. The implications of this are dire.
Even if murder is not the objective, it is entirely feasible that hackers can cause havoc by exploiting vulnerabilities to create a fleet of hundreds of “zombie autos” in a city. The hacker then can launch a denial of service attack that would bring a city’s highways to a standstill by making cars drive erratically and dangerously.
And the list goes on.
The ways that a hacker can kill are almost endless.
- Hacking the power grid
- Hacking a pacemaker or other medical device
- Hacking the water supply systems
- Hacking boat navigation systems
- Hacking weapons systems
- Hacking drones and using them as weapons
- Hacking prison systems to release prisoners
- Hacking nuclear power facilities
- Hacking the air traffic control system
- Hacking devices to make the overheat and explode
- Hacking traffic lights to cause accidents
- Hacking law enforcement reporting systems
Have hacker’s already committed murder? I think that the answer to this is likely yes. To be sure, in the future, the likelihood of such a crime will continue to rise.