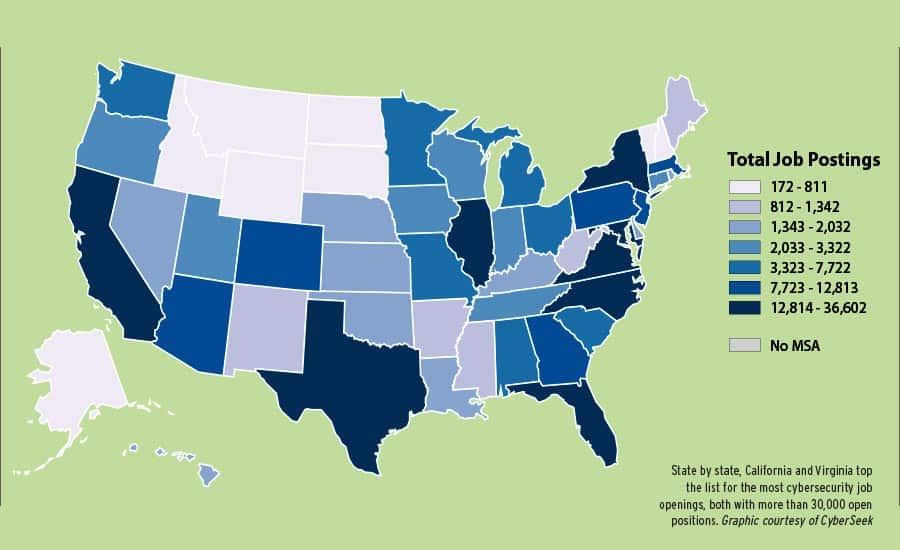
We analyzed the job postings, crunched the data, and determined the actual value of the CISSP certification to list the top 20 US cities for CISSP certification holders.
The monetary value of having the CISSP certification is dependent on your job market. If you obtain the CISSP certification and live in a city that has limited CISSP jobs available, then you need to make a choice – move to an area that has more opportunity or accept a salary that is not commensurate with your skills and abilities. Remote work is sometimes a possibility, but many cybersecurity positions require that the employees work on-site.
If you are trying to decide where to move to make the most money with a CISSP certification, this list is for you.
The Methodology
We complied raw data from job search portals to determine the average salary ranges from actual open positions. We compiled the data from LinkedIn, and Glassdoor, and other job websites. The data were analyzed and interpreted to create this list.
There is a margin of error in the data based on published job list salaries that are usually negotiable. Specific skill sets combined with the CISSP certification can demand a higher paycheck than in the published ranges. Some CISSPs with specialized experience will have the opportunity to earn far more than our calculated ranges.
The CISSP certification assumes that the holder has at least five years of experience in more than one cybersecurity domain. Given this experience requirement, holding a CISSP will assume that you also hold the required or preferred experience level for the positions we evaluated to determine job market value. This will not be the case for all of the jobs we looked at, but it is our general assumption.
Here’s the list:
#1. San Francisco CA
$100,100 to $145,700
San Francisco is one of the few job markets in which nearly all CISSPs earn an average of over $100K. The CISSP certification value is driven up by all of the technology companies around the silicon valley area. The cost of living is high in the area, but the pay is also great. With around 1000 open CISSP jobs in the area, there is always a demand. If you have a CISSP certification, then you will likely not ever be out of work in this technology hub.
Some of the companies who are actively seeking CISSPs include:
- Accenture
- First Republic Bank
- Cisco
- Salesforce
- Deloitte
#2. New York City
$95,000 to $145,000
A CISSP certification is precious in New York City, with the upper range of salaries for CISSPs near $150K per year. The value is determined by both the demand for cybersecurity experts and the cost of living in the area.
Major employers for CISSPs in New York include:
- Deloitte
- Accenture
- BNY Mellon
- Engineering Research Group Inc.
- EY
#3. Chicago IL
$90,000 – $140,000
The windy city has a high demand for CISSP, certified cybersecurity professionals. The salary range for CISSP positions in Chicago is just under that of New York City. With a cost of living that is more reasonable than many other cities, this is a prime city for cyber experts.
The major employers for CISSPs in Chicago include:
- Accenture (16)
- Request Technology
- Crowe
- Bank of America
- Deloitte
- Avanade
#4. Boston MA
$90,000-$135,000
Boston has a great job market for CISSPs. The low end of the market is similar to some of the other larger cities, but five years or more of experience will bring you a higher salary in the $135K range. The cost of living in this market is higher than average, but the town is alive with things to do.
Some of the companies who are actively hiring CISSP certified professionals include:
- Raytheon
- State Street
- BAE Systems
- Foreground Security
- Accenture
#5. Washington DC Metro Area
$90,000 to $130,000
A CISSP certification is valuable in the Washington DC metro area (Including Northern Virginia and Maryland). There are roughly 10,000 open advertised job positions in this region.
Major employers for CISSPs include:
- Booz Allen Hamilton
- CACI
- General Dynamics Information Technology
- ManTech International Corporation
- Perspecta
These companies are government contractors who hire people based on contracts that they win. The government defines the qualifications for the positions, and the qualifications are contractual. For many cybersecurity positions, the government requires the CISSP certification and other IAT Level 3 certifications to be considered for the job. Often a security clearance is required to be considered for government contracting CISSP positions.
#6. Los Angeles CA
$90,000 – $130,000
With consistently around 1000 open CISSP positions in the Los Angeles area, there is plenty of opportunity for cybersecurity experts. The salary range for CISSPs is comparable to the Washington DC metro area, but the cost of living in LA is a bit higher. If you are willing to fight the traffic and enjoy the weather, this is a great place to be a CISSP.
Major employers of CISSPs in the Philadelphia area include:
- Northrop Grumman
- Deloitte
- RSM US LLP
- Accenture
- Time Warner
#7. San Bernardino CA
$90,000 – $130,000
The San Bernardino area has a pay range similar to Los Angeles, but the demand for CISSPs is far less. However, there are consistently a couple of hundred CISSP job openings in this area.
Some of the companies in San Bernardino who are actively hiring CISSP certification holders include:
RSM US LLP
Accenture
Southern California Edison
Esri
Deloitte
#8. Pittsburgh PA
$90,200 – $125,100
Pittsburgh has been working to attract technology companies over the last ten years. The ‘Burg is the home to many technology companies now because the city offers generous tax incentives for companies to move to the area. With a couple of hundred job openings available consistently, this lower cost-of-living city may be for you. Go Steelers!
Some of the companies in Pittsburgh that are employing and actively seeking CISSPs include:
- Highmark Health
- BNY Mellon
- Software Engineering Institute
- Accenture
- EQT Corporation
#9. Minneapolis MN
$89,900 – $130,000
Businesses in the twin cities require CISSP certified professionals with several hundred open jobs consistently. If you want to work in this market, then the demand is certainly there, and the compensation range will allow you to live very comfortably.
Some companies in the Twin Cities area who are often looking to hire CISSPs include:
- Target
- Accenture
- UnitedHealth Group
- RSM US LLP
- Best Buy
#10. Atlanta GA
$87,500 – $130,000
Atlanta consistently has 300-500 job openings available for CISSP certified folks. The cost of living is reasonable, and there is plenty of growth in the industry. The summers are hot, but the winters are mild. Most would say that Atlanta is a great city in which to live.
Companies like the following are actively seeking CISSPs in the area:
- Fiserv
- Accenture
- E*TRADE FINANCIAL
- Ernst & Young OM
- Verizon
#11 Houston TX
$85,300-$135,700
The international city of Houston is a highly populated technology hub. This city is the home to many oil and energy companies like Shell, Exxon, and others. There are just under 800 open CISSP jobs in Houston and the surrounding areas.
Major employers in the Houston area include:
- Deloitte
- Accenture
- RSM US LLP
- Avanade
- General Electric
Houston is an attractive market to work in for the young professional. The city is vibrant, and the weather is hot! The job market for CISSP cybersecurity professionals is also hot.
#12. Baltimore MD
$85,000 to $125,000
Baltimore has many hundreds of open CISSP jobs available for the taking. This city is trying to make its name as a cybersecurity epicenter in the US. Cybersecurity is the focus of many companies in this area. The short commute to military bases and even the Washington DC area makes this city bloom for cybersecurity pros.
Some of the major companies who are actively seeking out CISSP certified workers include:
General Dynamics Information Technology
CSRA
Northrop Grumman
Johns Hopkins Applied Physics Laboratory
CyberLinx Solutions LLC
#13. St Louis, MO
$84,400 to $121,000
“The Gateway City” is not known for technology but still offers a comfortable salary for CISSP certified workers. Companies consistently advertise 100-200 openings for positions in this area that require the CISSP certification.
In St. Louis, some of the companies that seek out CISSPs include:
- AT&T
- CACI
- Spectrum
- Abile Group, Inc.
- ManTech International Corporation
#14. Detroit MI
$84,400 to $129,500
There are consistently 100 to 200 open CISSP positions in the Detroit area. As expected anywhere, the average salaries for a CISSP can be into the low six figures.
Companies that are actively hiring for CISSP positions in Detroit include:
- TARGET
- Accenture
- UnitedHealth Group
- RSM US LLP
- Best Buy
#15. Dallas TX
$84,100 to $130,100
The lower cost of living combined with great salary prospects makes Dallas a good place for CISSPs to work. There are just under 500 open jobs in this market, and the demand for cybersecurity experts is continuing to grow.
Major employers for CISSPs in the Dallas area include:
- Verizon
- Raytheon
- Grant Thornton
- Bank of America
- Ernst & Young OM
Dallas is a technology hub. More and more technology companies are moving to this area for lower commercial real estate costs, tax advantages, and a great pool of technology workers. Verizon has a large campus just west of the city. Apple has a presence here and recently announced a large expansion of its workforce in this area.
#16. Denver CO
$84,000 – $125,000
The Denver area has several hundred open CISSP jobs at any time of the year. The salary range for these positions can get into the low six figures. If you love the outdoors and have the CISSP certification, then Denver may be the city for you!
Companies in the Denver area that regularly hire CISSPs include:
- Lockheed Martin Corp.
- AppliedTrust
- Accenture
- Raytheon
#17. Miami FL
$80,100 – $120,600
Miami has plenty of demand for CISSP cybersecurity professionals. The cost of living is a bit lower than many major cities, and the average salary for these positions is about $100k.
Some of the employers in this area who hire CISSPs include:
- Enterprise Risk Management
- ADT Security Services
- ADT Corporation
- Citi
- Verizon
#18. Phoenix AZ
$81,500 – $122,000
If you like hot desert weather, Phoenix can be a good choice for the CISSP certified professional. Phoenix has a low cost of living, and the CISSP certification demands a nice salary in the area.
Major employers for CISSPs in Phoenix include:
- Vitalant
- Productive Data Solutions, Inc.
- Early Warning Services
- Wells Fargo
- Paypal
#19. Tampa FL
$80,100 – $120,000
The Tampa area is quite inexpensive when compared with other major US cities. Given this, having the CISSP certification can earn you well over the average wage for a very comfortable lifestyle.
Some of the employers in the Tampa area who are actively hiring CISSPs include:
Verizon
RAYMOND JAMES FINANCIAL
PwC
Nielsen
RSM US LLP
#20. Omaha NB
$75,100 – $121,200
Omaha has a bit lower of a salary range than the larger cities, but there is still a market for cybersecurity professionals in the area. With both government and private sector opportunities available, we found about 500 open positions that require the CISSP certification.
Major employers for CISSPs in Omaha include:
- TD Ameritrade
- G4S
- Oasis Systems, Inc.
- LTi Technology Solutions
- SAIC