Password change best practices are essential to securing sensitive data for both individuals and businesses. A robust password change policy is necessary to ensure sufficient defense against hackers, scammers, and security threats. Implementing best password protection practices is regarded to be an essential front-line defense. The rules protect critical information and IT infrastructures from unauthorized access to preserve integrity, availability, and confidentiality.
Whereas organizations have made long strides in other authentication methods, such as biometrics and certificate-based authentication, passwords remain among the most widely used techniques. At least 71% of users use password security to secure various accounts. However, there are numerous security challenges as malicious cyber actors innovate better ways of compromising password security. Password change policy best practices should be a top concern for all organizations. It is necessary to understand password security threats to appreciate the need for password change policy best practices.
Common threats to password security
Dictionary attacks: Hackers execute dictionary attacks using a software program that automatically inputs a list of common words in a pre-arranged listing. Cracking software creates a variation of common passwords to increase the success rate of compromising user passwords.
Hacking security questions: Many individuals use the names of relatives, spouses, children, pets, or attended schools as the answers to security questions. Hackers can guess such details when trying to crack a password through a reset process. A little research on social media can provide the information needed to break security questions.
Guessing simple passwords: Cybercriminals are aware most people use a sequence of letters or numbers to create a password. Examples are 123456, qwerty12345, 1qaz2wsx, among others. Using such passwords threatens the security of an entire organization.
Compromising accounts with the same password: Most people tend to reuse the same password across multiple accounts. A breach that compromises one account (See How Does Email get Hacked?) can enable a cyber adversary to access all other accounts using the same password. Reusing a password for social media accounts, banking, email, and work accounts may lead to additional security threats, such as identity theft.
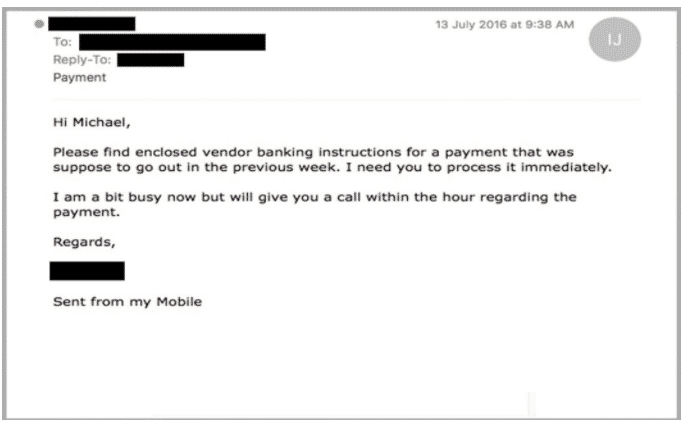
Social engineering: Social engineering is among the oldest techniques used to compromise password security. Social engineering is a method where hackers manipulate their victims into performing actions, such as divulging protected information. The information includes a password used to secure confidential data and critical systems.
Recent password security statistics
-
Over 300 billion passwords will be in the market by 2020
A recent report predicts that there will be more than 300 billion passwords by the end of 2020. The report attributes the staggering numbers to the growing use of password protection among artificial intelligence and humans. As a result, an average user could be managing approximately 60 to 90 different numbers. Companies and individuals should take such a large number as a warning that reusing passwords or creating weak passwords could result in increased cases of cyber vulnerabilities.
-
Cyber-attacks are the fastest-growing crimes.
Cyber-attacks are among the fastest rising crimes globally in 2020. The rapid growth should be a massive concern for the private and public costs since the cyber-crimes result in skyrocketing costs. Since financially motivated attacks account for 71% of sensitive information leaks, while 25% are related to spying, cybercrime costs could exceed $5 trillion in the coming years. Such numbers are worrying since password reuse and creating weak passwords cause 81% of attacks and data breaches.
-
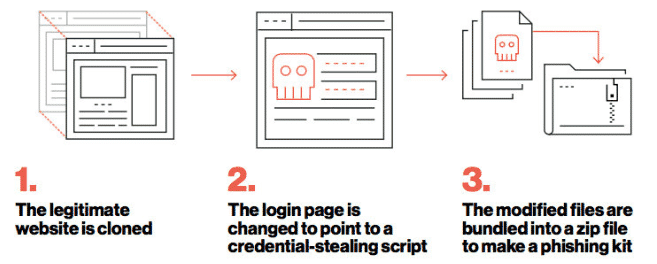
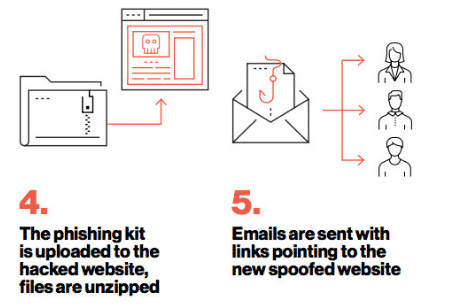
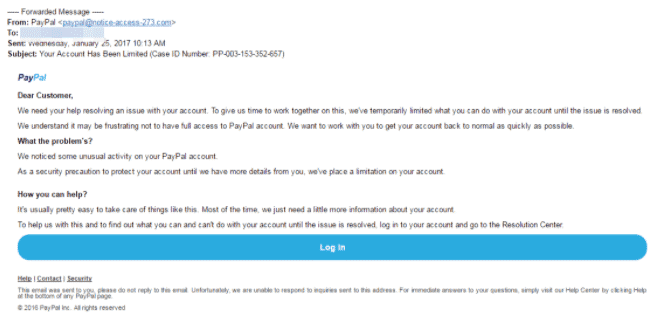
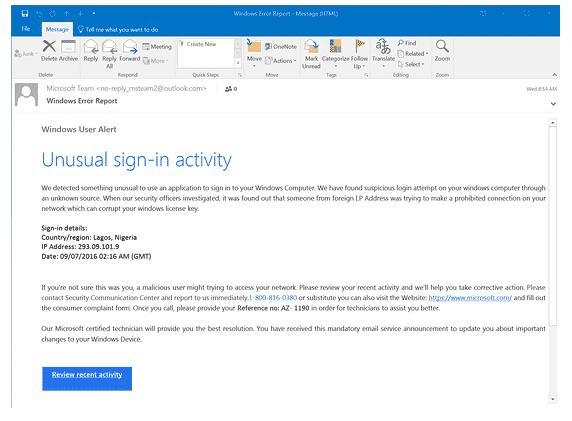
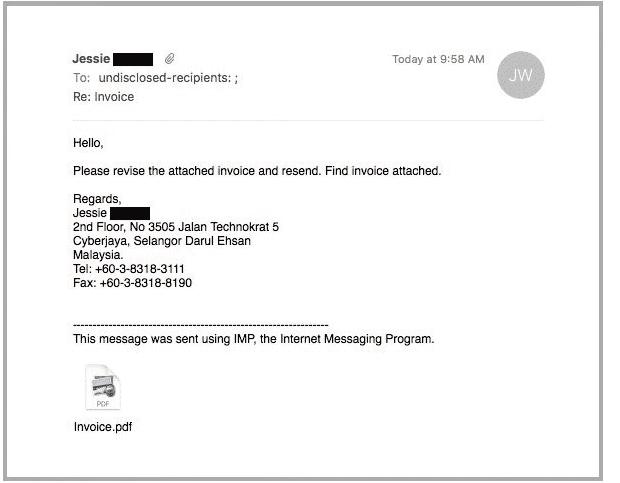
Phishing and spam are among the most widely used methods for compromising password security.
In 2019, at least 76% of businesses were victims of phishing and other related social engineering attacks. Cybercriminals use fraudulent emails, links, and attachments to trick unsuspecting users into revealing confidential information like passwords and credit card details. Although many employees are aware of social engineering attacks, they still click on malicious emails, links, and attachments. The actions put a company’s systems and data at dire risk.
-
Human errors account for most attacks.
Human mistakes are one of the most challenging issues to detect and prevent. Statistics show that human errors contribute to 52% of attacks and data breaches. Employees can make mistakes due to an inadequate understanding of cybersecurity literacy. Common mistakes made in password security include sharing unencrypted passwords over insecure networks, reusing passwords across different accounts, and creating weak passwords to protect confidential information. As the number of cyber-attacks increases in 2020, it is prudent for companies to give special consideration to the team and individual password security practices.
The 2019 State of Password and Authentication Security Behaviors Report compiled the following results obtained from a survey drawing 1,761 IT security practitioners:
- 51% of users reuse passwords in personal and business accounts
- 69% share their passwords with other colleagues
- 67% of users do not use multi-factor authentication in their personal passwords, while 55% don’t apply the authentication scheme in their work passwords
- 57% of users who have encountered a phishing attack did not change their password behaviors
- 57% prefer using login methods that don’t involve password protection
Top Password Change Policy Best Practices
-
Require Employees to Create a Long, Strong Passphrase
Creating strong passwords makes it harder for cybercriminals to crack them using brute-force, dictionary, and other types of password attacks. Strong passphrases must contain at least eight characters, consisting of lowercase, uppercase, symbols, numbers, and letters. The National Institute of Standards and Technology (NIST) advocates for creating long, easy to remember, and difficult to crack passphrases. According to the NIST Special Publication 800-63, a recommended password change policy best practice involves generating passwords with at least 64 characters maximum length. The characters should include spaces.
-
Use Password Encryption
Using encryption technologies ensures passwords are protected. Organizational employees should use cryptographic methods to secure stored passwords and encrypt passwords shared over a network. Encryption ensures the passwords are inaccessible even if they fall into the hands of unauthorized individuals. The best password change practice to consider is implementing nonreversible, end-to-end encryption. The encryption ensures employees share passwords securely.
-
Use Multi-Factor Authentication
Multi-factor authentication has become a crucial standard for measuring access privileges to protected resources. A multi-factor authentication scheme requires users to provide additional details to verify their legitimacy and authenticity. In addition to the usual credentials, such as passwords and correct usernames, users must confirm they are legitimate by providing additional items sent to a specified device. The items can be a code, biometric verification, or a personalized USB token. Multi-factor authentication prevents malicious individuals from using stolen password credentials to access protected data and systems. The idea is that by using multi-factor authentication, cracking or guessing passwords alone cannot enable attackers to gain unauthorized access.
-
Test New Passwords
Most users create new passwords and leave it at that. While changing passwords is a health practice for maintaining password security, there is a probability of using an already compromised password without knowing. Since criminals use a list of known passwords when executing dictionary attacks, creating a compromised password exposes the protected resources to unauthorized access instances. As such, organizations should require their employees to test new passwords using online testing tools. The tools also determine if a password can be hacked easily. An example of such tools is the Microsoft password strength checker.
-
Avoid Using Dictionary Passwords
Dictionary passwords are user credentials created using dictionary words. Currently, there are 171,476 usable words in a dictionary. Hackers develop sophisticated and powerful software programs capable of cracking passwords by inputting several words a second. The software programs also generate a variation of each word to increase the success rate. As such, software running a dictionary attack can end up trying millions of combinations until a hacker finds the correct password. Employees should avoid using dictionary words to create passwords. Instead, they should use various random characters, including alphabetical letters, special characters, and numbers, to create a long passphrase.
-
Use Different Passwords for Each Account
Using different passwords is one of the most recommended password change best practices. Reusing a password in other accounts exposes them to the dangers of unauthorized access since a hacker will require to compromise the security of one account. In particular, employees should restrain from using a single password to secure their work accounts. A password manager is a suitable alternative to reusing passwords. Individuals can create a strong master password to secure all other passwords stored in a password manager tool. It requires users to remember the master password only to access the stored passwords.
-
Change Passwords Only When There is a Potential Compromise or Threat
A long-standing password security practice forces employees or system users to change their passwords after some time. However, recent NIST password security guidelines advise against enforcing a password change policy, citing various reasons. The reasons include that forcing periodic password changes makes users repeat previous passwords to avoid remembering new ones. Reusing passwords is a security threat. Also, frequent password changes may cause employees to write down the new passwords if they forget them. However, written passwords may be accessed due to failing to adhere to a clean desk policy. Therefore, organizations should only request employees to change their passwords only when there is a potential threat or compromise.
-
Change the Credentials for Accounts Not in Use
Companies must ensure to change the login credentials of accounts no longer in user. The employees assigned the accounts could be transferred to a different department or terminate their employment with the organization. Failing to change the password credentials of idle accounts exposes an account to various threats. For example, disgruntled employees could access the account and commit malicious actions on a company network or steal sensitive information due to revenge motivations. Also, insider threats could use inactive accounts to facilitate cybercrimes to cover their tracks. System admins must ensure all accounts that are not in use are disabled or have login credentials known to trusted individuals only.
-
Enhance the Security of Privileged User Accounts
Passwords used to secure privileged accounts require special security considerations. Privileged accounts are user accounts that contain higher privileges compared to ordinary user accounts. For example, they can remove or install new software, modify an application, network, or system configurations, or upgrade an operating system. Privileged accounts have far-reaching consequences if unauthorized actors gain access. Therefore, the passwords used to secure privileged accounts need special protections. They include changing the password immediately after use and restricting access permissions to one or two trusted individuals. /
-
Enforce a Password History
Although repeating or using passwords exposes critical systems to multiple threats, most companies have not implemented measures for curbing the vice. Enforcing a password history policy prevents a user from using a password used previously. A password history policy prevents users from reusing a specified number of previous passwords. For example, a company can create a policy where employees can not repeat twenty previous passwords. The policy protects against password hacking since it requires users to create new passwords each time they want to change old passwords.
-
Create a Password Audit Policy
Password policies enable a company to keep track of all recent password changes. The policy allows system admins to monitor password changes in a user account. Password audits are essential since they facilitate the identification of suspicious password habits. For example, accounts where passwords are changed a few times every day, could mean malicious intent. Moreover, a password audit policy assists in identifying account users not adhering to password change best practices. Identifying such users enables an organization to implement more robust password policies to maintain high-security levels.
-
Secure End Devices
End devices, such as smartphones, are used to reset account passwords or for multi-factor authentication. Failing to secure the end devices allows anyone with access to use them to hack or manipulate passwords. Individual users should ensure end devices have sufficient security to safeguard password protection. Strong passwords, or alternative methods like biometrics, should be used to secure end devices that can enable changes or modifications of passwords used to protect confidential accounts.