These 10 esential cloud security best practices are essential for any organization that is moving to the cloud. Overlooking any of these practices could lead to a security disaster.
Cloud computing has indeed revolutionized the business and technological landscapes. Today, it is unheard of that any serious company would prefer onsite IT infrastructure to cloud services. Simply defined, cloud computing is a technology consisting of networked remote servers. Service providers use the network to provide cloud consumers with data storage units and computational software programs for processing and managing data. An internet connection provides access to cloud technologies, meaning that users can access them from their workplaces or the comfort of their houses.
Currently, at least 90% of organizations use different cloud services, whereas experts indicate that companies will run 60% of their operations in the cloud by the end of 2019.1 This shows that cloud technology is already mainstream. However, cloud services are online-based, and this has caught the attention of all hackers. Increased dependence on cloud services to store and manage sensitive data is enough motivation for attackers. All companies and users, therefore, need to understand the best security practices to ensure they adequately protect their cloud environments. Here are the top ten internationally accepted cloud security practices.
Cloud Security Best Practices #1: Securely manage your data
Data security should be the topmost concern of all cloud users. To achieve optimum data protection, first, identify data with the most classified information. Highly sensitive data require stronger security. Some would, however, prefer applying high-level security to all cloud data. This might not be sufficient due to factors like data size and format, i.e., audio, visual, print, etc. Besides, information like patents and intellectual property cannot be secured the same way as business ledgers. Or personally identifiable information, for that matter. Some types of data must be protected at all costs due to their value and importance to the organization. A data classification software can assist in determining the data requiring stronger security.
Then, implement a comprehensive security solution. It should be capable of locating sensitive information in the company’s network, databases, endpoints, and cloud storage units. The solution should provide security but not at the expense of flexibility and data access. As much as this is true, the data access and storage procedures should be a priority. A Cloud 2019 Adoption and Risk Adoption Report by McAfee shows that 21% of data managed in the cloud has sensitive content.2 All cloud service providers, including Office 365 and Salesforce, don’t guarantee the data will be 100% secure. It is hence, essential to continually review and update access permissions associated with the data. Some instances might require a business to remove or quarantine highly sensitive data.
Also, a company must enforce strict data sharing policies. In 2019, there has been a 50% increase in the sensitive data shared through the cloud.3 The risks of malicious insiders or hackers accessing and stealing or corrupting cloud data are too high. In spite of whether a company has applied powerful mitigation strategies, it must establish sufficient access controls for any data stored and accessed through the cloud. For instance, users requiring to edit data might be fewer than those needing to view it. As such, access controls should be tailored to suit the permissions for each employee.
More importantly, banking on the cloud provider’s data encryption techniques would be a grave mistake. Although the offered encryptions prevent unauthorized users from accessing the data, the service providers can access the encryption keys and decrypt it at any time. As such, full access control means deploying stringent encryptions and using adequate public key infrastructures.
Cloud Security Best Practices #2: Implement endpoint security
Using the services or applications of a particular cloud provider doesn’t disregard the need for using robust endpoint security. Endpoint protection means securing end-user devices, such as laptops, desktops, and mobile devices. Companies need to protect endpoints to their corporate networks and for devices used to access their cloud accounts. This is because they serve as access points to all cloud processes, and malicious actors can exploit them at any time. Enhancing endpoint security allows a company to prevent risky activities that can provide entry points. Besides, enforcing endpoint protection and compliance as per existing data security regulations enables a business to maintain stronger control.
Notwithstanding, endpoint protection affects cloud security due to the growing access points to a cloud. Increasingly, organizations improve their operations by incorporating practices for accessing data more fluidly. For example, they implement BYOD (Bring Your Own Device) policies where employees can use their personal devices to access and modify cloud data. The devices require adequate endpoint security such that they can’t provide hackers with easy targets for stealing or corrupting data. Such include using VPNs when accessing cloud accounts via a public Wi-Fi network.
Furthermore, cyber adversaries nowadays prefer to breach a network or data security through endpoints. This is unlike in the past, where most breaches were done through a network. As a result, depending on a centralized network security solution may be insufficient. The increased used of the Internet of Things in managing cloud activities comes with increased risks since they also grow the possible entry points. A growing reference for breaching security through endpoints requires more focus on endpoint security.
But what are the various solutions that can enable a cloud user to maintain optimum security? The first and most basic is using password protection. All users need to secure their devices with strong passwords to prevent malicious users from accessing. Also, employees should avoid sharing the devices used for work reasons. An innocent user can accidentally delete all data stored in the cloud. More so, all devices should contain malware scanning tools to scan USB sticks or hard drives before they connect to a corporate network. This lowers the risks of a hackler introducing malware through endpoints.
Cloud Security Best Practices #3: Carefully choose the cloud vendors
All cloud service providers try their best to enforce cloud security measures to attract more customers. Some vendors may even contain better security compared to the one which in-house staff maintains. However, some may claim to have the best protection as a marketing tag while in the real sense, they have poor security schemes. To this end, Chief Information Security Officers (CISOs) of every organization have the responsibility of assisting their employers in using the most secure vendors. Some companies may even need to use vendors that implement security policies to mitigate industry-specific threats.
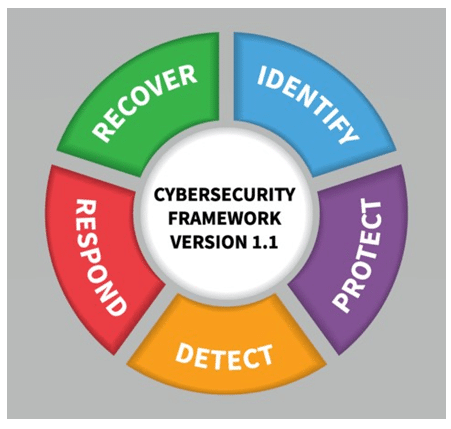
To choose the most secure cloud providers, organizations can use various factors to assess their security capabilities. Such include evaluating their levels of compliance with various information compliance standards. Different regulations, including GDPR and HIPAA, advocate for organizations to implement different requirements, all aimed at achieving data security. To ensure cloud service providers are fully compliant, a business should require them to produce compliance certifications. Certification means the providers satisfy all requirements of a compliance audit. Also, cloud vendors should demonstrate they can ensure 24/7 data and network availability. Data drives critical operations; thus, cloud providers should maintain multiple backups.
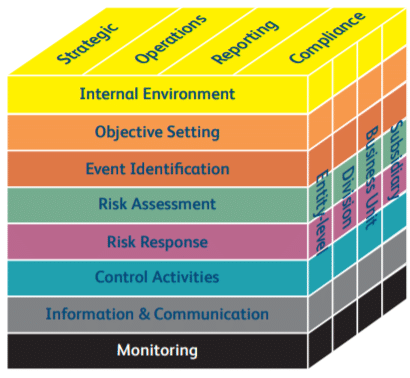
Additionally, a company should only subscribe to a cloud provider that conducts regular risk assessments. Assessing their servers and IT infrastructure for security risks enables cloud providers to apply mitigation strategies before hackers can exploit them. Risk assessment and management is a crucial cybersecurity operation that every cloud provider should observe. Lastly, an organization needs to use the services of a cloud vendor that indicates the customer’s responsibility in matters of security. Cloud security is a collaborative process where both the providers and the customers must play their roles to ensure optimum safety. For instance, a cloud provider should install timely patches to prevent attacks such as zero-day attacks. Customers, on the other hand, should develop security policies governing access, sharing, and modification of cloud data.
Cloud Security Best Practices #4: Monitor and prevent
As previously mentioned, the consumers and cloud service providers have different roles when securing cloud activities. They also share the responsibilities for monitoring and responding to suspicious cloud security problems. The cloud vendors monitor the security of infrastructures they use to provide services to cloud consumers. On the other hand, the customer monitors the applications and systems various users use to access the services. Also, service providers tend to provide customers with monitoring information relating to the services they use. Relying on the monitoring information can enable a company to implement measures for detecting incidences of unauthorized access. They can also use the information to monitor for unexpected behavioral changes in regards to a user’s interaction with cloud data and applications.
It is also vital that a company implements additional monitoring that fully integrates with cloud automation. Cloud providers implement automation schemes such as autoscaling to provide users with round the clock access to more resources as per their needs. Implementing integrative monitoring provides 100% visibility onto all cloud resources. As a result, consumers can quickly detect unusual occurrences and address them to prevent security problems.
Besides, as with all other operations, collaboration is critical. Cloud vendors monitor IT infrastructure used to provide services and computation resources. Such include entire SaaS applications, networks, IaaS like storage units, and virtual machines. The service providers may detect activities that could adversely impact a consumer’s cloud data or applications. In effect, the provider may need to inform a customer of the activities so that they can coordinate an adequate response.
Similarly, a cloud user may detect other activities that they cannot address without the input of the service provers. Responding to any security event requires both providers and consumers to share the responsibilities. Effective collaboration means understanding the limits of a cloud provider in monitoring and responding to security incidences, such that a provider cannot be caught unawares.
Cloud Security Best Practices #5: Conduct due diligence
Cloud consumers need to understand the applications and networks of their cloud providers fully. Understanding them can enable a company to provide resiliency, security, and functionality for systems and applications deployed in the cloud. As such, they must perform due diligence across all lifecycles of deployed systems or applications. During the planning phase of a cloud migration, companies should select suitable cloud applications or service providers to move to. Benchmarking on other organizations that use the services of a particular cloud provider can provide valuable information. First-time cloud deployments can use the information to determine if a service provider implements security policies that meet their needs.
Also, a cloud consumer should always use the provider’s guidance and documented best practices for using applications and provided services. For example, developing a cloud-based application should follow the cloud service provider’s guidelines and security practices. Also, when migrating to an already implemented cloud system or application, reviewing its documentation and collaborating with the vendor can provide insightful information on how to securely use it.
More importantly, cloud providers abstract service to optimize resource usage and access. Abstracted services might resemble physical applications, networks, and hardware. Consumers need to understand that abstracted services or resources have different security practices or policies compared to those implemented on physical resources. Before subscribing to their usage, organizations can observe security by reviewing and understanding security approaches implemented on the virtual resources. These should guide the processes through which users access them.
Besides, deploying or developing applications for cloud use must need companies to enforce policies to ensure users operate them securely. In contrast to physical resources like disks, networking devices, and servers, cloud consumers use software to interact with virtualized resources. Software security practices like patch management and vulnerability testing should, therefore, guide all cloud-access activities.
Cloud Security Best Practices #6: Implement intrusion detection and prevention systems
A survey from CloudPassage indicates that intrusion prevention and detection systems are the third most effective solutions for cloud security.4 The systems monitor cloud and corporate networks for intrusion signs and prevent unauthorized access. Additionally, they immediately alert a security administrator of the attempts, thus allowing the deployment of mitigation solutions. More so, intrusion detection and prevention systems are capable of implementing responses to intrusion attempts. Such responses include preventing and blocking access from the source of the attempted intrusion.
Also, an organization can consider implementing artificially intelligent prevention and detection systems. Artificial intelligence learns the behaviors of all user-activities accessing a particular cloud environment. For example, it builds knowledge of the types of data an employee uses frequently and the types of cloud resources the employee requests. Hence, whenever a new user performs unusual activities, the system flags him down as a malicious entity, preventing him from accessing any more requests. As such, the intrusion risks of a malicious insider assuming the identity of a legitimate user are minimized.
Furthermore, intrusion detection and prevention systems minimize the number of generated false positives. These are false alerts that a system raises as intrusion alerts. False positives can be due to the assignment of new roles to a user, which can lead to an intrusion prevention and detection system alerting as suspicious activities. False positives can cause a company to invest in unnecessary measures as the alerts turn out to be false security alerts.
Cloud Security Best Practices #7: Define cloud usage policies for all employees
Although organizations implement a corporate strategy for securely using cloud accounts, employees tend to utilize the clouds without adhering to the implemented strategies. For example, they might fail to inform the relevant stakeholders when they transfer or modify cloud data. Therefore, monitoring their usage activities is a crucial aspect of maintaining cloud security. Monitoring provides a clear picture of the services or resources a particular employee accesses and their usage patterns. Users with suspicious cloud usage activities can be denied access to ensure they don’t introduce security risks to cloud data and applications.
To determine the risk levels a particular user poses to cloud security, an organization can assess the network firewalls, logs captured in the security information and event management system, and web proxies. Then, the assessment results can enable security personnel to obtain the value of the risk levels towards organizational security. The obtained values can help determine whether a particular user should have complete or partial access to an organization’s cloud accounts.
Furthermore, cloud consumers must understand that that shadow usage not only refers to unauthorized access to cloud services using endpoints, but it also entails moving data from trusted environments to unmanaged devices. Such practices endanger data security and threaten to impact data availability, integrity, and confidentiality. As such, a data officer should authorize data movement within the cloud and keep track of the data accessed from a particular endpoint.
#8: Maintain a safe list
Most employees within an organization use cloud services to meet the company’s goals and objectives. However, a few employees often use organizational clouds for their gains. Using cloud services for dubious services places a company danger of the cloud’s security being compromised or facing legal tussles due to compliance issues. As such, a business should develop and maintain a safe list for all the services employees can access through their cloud accounts. Enforcing the list and ensuring employees are aware of minimizes issues arising from compliance penalties or insecure practices.
In any case, establishing a safe list enables an organization to specify the data each employee can access. It also ensures an employee understands the data permitted to be processed through the cloud. Creating such awareness leads to effective data management as all users are aware of the data they can use or share through cloud platforms. Similarly, a safe list provides all cloud users with a list of applications they can use in a cloud environment. Lastly, a safe list provides a clear outline of the security practices to observe when interacting with cloud data or applications.
#9: Trust users, but verify
Cloud consumers should adopt additional verification procedures to supplement other security practices like password protection. Verification schemes protect a cloud environment from malicious activities perpetrated by malicious users assuming the identity of the legitimate users. An effective verification scheme is the use of two-factor or multi-factor authentication. The authentication mechanisms require cloud users to provide additional items of proof that they have authorized access to cloud data. Such items can include a code sent to a trusted mobile number or the answer to a security question only known to the user. Such provide a strengthened cloud security posture.
In addition to the different authentication mechanisms, a company must ensure that authenticated users have the authority to access and interact with cloud data. Whereas an employee might pass a verification process, he might lack the permissions to access particular types of data and cloud applications. Several access controls can be used, including least privilege access, role-based access, among others. Organizations should control data access to eliminate risks associated with unauthorized access. Investigations should be conducted on attempted unauthorized access by tracking the endpoint used in the attempted intrusion.
#10: Regulatory compliance boosts security
A cloud consumer has a role in ensuring full componence with information security regulations. Although many businesses adhere to compliance regulations to avoid non-compliance fines, the security requirements recommended by various standards enhance security. Therefore, implementing the guidelines is an effective way of tackling security issues. More importantly, companies require to understand that the compliance regulations designed for cloud providers differ from those meant for consumers. As such, they shouldn’t fail to adhere to recommended security practices with the notion that cloud providers have already complied.
Moreover, outsourcing compliance responsibilities is not recommended, despite the business functions shifted to the cloud. Also, identifying a cloud provider with a platform that facilitates compliance is a plus for cloud security. This allows a business to fully comply with regulations such as HIPAA, GDPR, PCI DSS, among others. Understanding the compliance aspects can facilitate optimum security of a particular company. Lastly, automating compliance can eliminate the problems associated with tracking new or updated compliances. Automating compliance processes ascertains a cloud consumer keeps track of all regulations such that it covers all security aspects. Various companies develop automated compliance software programs designed to meet all organizational needs. All the recommended practices can assist cloud consumers in achieving maximum security.
1 https://hostingtribunal.com/blog/cloud-computing-statistics/
2 https://www.mcafee.com/enterprise/en-us/solutions/lp/cloud-adoption-risk.html?_ga=2.224418842.1031089963.1568031446-47850940.1568031446
3 https://securingtomorrow.mcafee.com/business/cloud-security/top-19-cloud-security-best-practices/
4 https://www.esecurityplanet.com/network-security/intrusion-prevention-systems.html