The purpose of this Types of Cybersecurity Guide is to provide a simple framework for integrating cybersecurity activities and give a brief overview of the security controls that should be exercised.
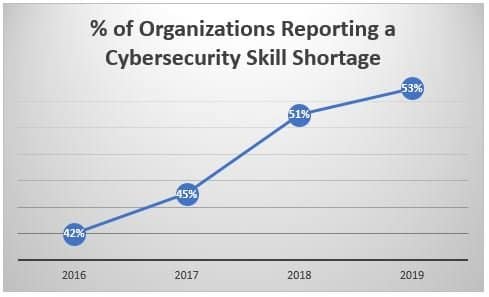
Cybercrime is a growing concern in the digital environment. Most smaller companies do not have their own cyber security teams and cybercriminals who seek financial or business benefits are likely to target these smaller and more vulnerable targets.
This Types of Cybersecurity Guide contains the different types of cybersecurity and their safeguards. We have compiled a list of 12 cybersecurity themes, along with basic and advanced recommendations that will help protect against data breaches and cyber-attacks.
12 Types of Cybersecurity / Cybersecurity Themes:
ENGAGE TOP MANAGEMENT
Involving top management in the project is essential to creating a sustainable training strategy throughout the organization.
BASIC PROTECTION
- Designate an information security officer.
- Identify your ICT risk and protect your business for the future.
- Comply with legal and regulatory requirements regarding privacy, data processing and security.
- Be aware of cyber threats and vulnerabilities on your networks.
ADVANCED PROTECTION
- Make sure the information security officer is an independent agent who is not part of the IT department.
- Clearly define the objectives of system and network monitoring.
- Identify the legal consequences of a data leak, a network failure, etc.
- Periodically conduct a risk and security audit. Communicate the results and the action plan to management.
DEVELOP A SECURITY POLICY AND A CODE OF CONDUCT
This is a set of rules, laws, and practices that must be followed in the workplace. It is based on existing risks and aimed at making management and employees more accountable for the prevention of security incidents.
BASIC PROTECTION
- Create and apply procedures for the arrival and departure of users (staff, trainees, etc.).
- Describe roles and responsibilities for security (physical, personnel).
- Develop and distribute a code of conduct for the use of computing resources.
- Schedule and run security audits.
ADVANCED PROTECTION
- Create a classification scheme and traceability of sensitive information.
- Introduce the notions of “need to know”, “least privilege” and “segregation of duties” into your corporate policies and processes.
- Publish a responsible disclosure policy.
- Store sensitive documents in locked cabinets.
- Destroy sensitive documents with a shredder.
- At the end of the work day, destroy the documents left on the printer.
- Apply Locked Print if available.
- Develop a concept and training plan for cybersecurity.
SENSITIZE YOUR WORKERS TO CYBER RISKS
Workers are the weakest link in the information security chain. Make your internal and external employees aware of information security risks. Make sure they understand your messages and test their knowledge. They will be your first line of defense in case of attack.
BASIC PROTECTION
- Inform your users to your code of conduct. Regularly remind users of the importance of safe behavior.
- Regularly remind users that information should be considered sensitive and handled in a manner that respects the rules of privacy protection.
- Inform users about how to recognize phishing (e-mail fraud) and how to react.
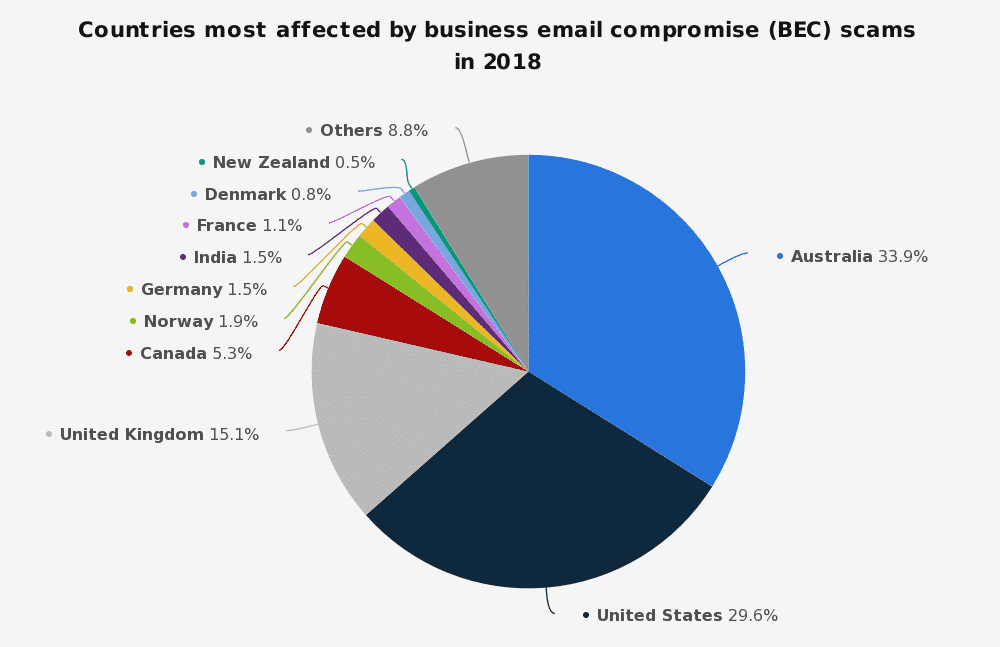
- Inform accounting staff about the phenomenon of “CEO fraud” and provide for control procedures in connection with the execution of payments.
ADVANCED PROTECTION
- Integrate knowledge and respect of the code of conduct into staff evaluation.
- Periodically evaluate user awareness and responsiveness.
MANAGE YOUR IMPORTANT COMPUTER RESOURCES
It is obvious that securing important data is a central issue for all businesses today. There are multiple threats to information systems and most company systems contain crucial private information.
BASIC PROTECTION
- Inform about the importance of all equipment and software licenses.
- Keep a detailed and up-to-date map of all your networks and interconnections.
ADVANCED PROTECTION
- Use a configuration management tool (or at least one tool such as Microsoft MMC, etc.).
- Define a basic security configuration.
- Make sure that Service Level Agreements and other Agreements have security clauses.
- Implement a change control process.
- Implement a uniform level of security for all your networks.
- Regularly audit all configurations (including servers, firewalls, and network components).
UPDATE ALL PROGRAMS
Updates play an important role in protecting your devices as they can fix errors or fix security vulnerabilities. They also give you access to the latest software features and design improvements.
Take the example of an antivirus: An antivirus is software that can fight against computer attacks, malware, and for the security of your device (computer or smartphone). This software must be regularly updated because new computer viruses are constantly being created.
BASIC PROTECTION
- Introduce an internal culture of the “patch” (workstations, mobile devices, servers, network components, etc.).
- Perform security updates of all software as soon as possible.
- Automate the update process and audit its effectiveness.
ADVANCED PROTECTION
- Set up a test and reference environment for new patches.
- Update all third-party software, such as browsers and plugins.
- Perform a full backup for the servers before the update and create emergency repair disks after the update.
INSTALL ANTIVIRUS PROTECTION
This is a crucial step to protect your personal data!
Your computer or device contains a lot of files and data about you. This includes photos and text documents (pay slips, taxes, scans, etc.). It also includes your browsing data.
This data can be used to exploit certain sensitive data that could lead to the theft of your digital identity. Examples of this include spoofing your identity using your private information including your phone number, email, photos, etc.). This spoofing may be used to harm you financially or harm your reputation.
Viruses spread to both computers and smartphones (iOS or Android). They also can affect tablets and other devices.
It is necessary to ensure that all of your devices are protected by antivirus software.
BASIC PROTECTION
- Antivirus software is installed on all workstations and servers.
- Antivirus updates are automatically done.
- Users know how antivirus software alerts you of a viral infection.
ADVANCED PROTECTION
- All virus alerts are analyzed by an ICT expert.
- Antivirus software is installed on all mobile devices.
- Antivirus is regularly tested using the EICAR test.
SAVE ALL INFORMATION
Your company’s employees exchange sensitive documents internally and externally on a daily basis. For legal, strategic, and security reasons, your data must be regularly backed up. It is prudent to engage a solution provider for your backup strategy. A trusted provider can ensure that your data is backed up and can assist with restoring data.
Data security is not just about adopting a backup solution. You should establish a data backup policy within your organization and establish procedures that must be followed by all employees.
BASIC PROTECTION
- Back up your important data daily.
- Host your backup solutions on your own servers or in the cloud.
- Back up backups offline and in a separate location (if possible, away from their source).
ADVANCED PROTECTION
- Backups are stored in a vault or in a secure data center.
- Periodic restore tests are performed to evaluate the quality of backups.
- Encrypt data stored in the cloud.
MANAGE ACCESS TO YOUR COMPUTERS AND NETWORKS
In the workplace, all computers connected to a server can be considered to be part of the network. You are responsible for the security of this vast system and you must defend the network against intruders. You must also ensure the integrity of data on computers inside the network.
Maintaining the physical security of your computing environment is essential to protecting your systems. Any system that is connected and left unattended is vulnerable to unauthorized access.
The areas around the computer and the computer hardware must be physically protected from intruders and unauthorized access.
You must also prevent unauthorized connection to a system or network by assigning a password or connection control. All accounts on a system must be password protected. While a password is a simple authentication mechanism, it protects the entire network from intruders. A strong password will protect against brute force attacks.
BASIC PROTECTION
- Change all default passwords.
- Nobody has administrator privileges for daily tasks.
- Keep a limited and up-to-date list of system administrator accounts.
- Passwords must be at least 10 characters long (a combination of character types) and must be changed periodically or whenever there is a suspicion of compromise.
- Use only individual accounts and never share your passwords.
- Disable unused accounts immediately.
- Make authentication and password rules mandatory.
- Rights and privileges are managed by user groups.
ADVANCED PROTECTION
- Users are only allowed to access the information they need to perform their missions.
- Detect and block unused accounts; Use multi-factor authentication.
- Block access to the Internet from accounts with administrator rights.
- Detect irregular access to information and systems (delays, applications, data, etc.).
- Frequently audit the central directory (Active Directory or LDAP directory).
- Limit worker access with a badge system and create multiple security zones.
- Save all visits.
- Organize office cleaning during working hours or under permanent supervision.
SECURE WORKSTATIONS AND MOBILE DEVICES
The number of threats on smartphones continues to grow. Android devices are especially targeted by hackers. All users are at risk and business users are heavily targeted.
The business workstation is also a common target for computer attacks. Implementing simple and quick tips for protecting your employees’ workstations is one of the most important steps you can take to secure your infrastructure.
Poorly protected workstations are a vulnerability that hackers look to exploit to gain personal data. Workstations can also become gateways for attacks on more sensitive systems within the company. There are some simple steps to apply to guard against these risks.
BASIC PROTECTION
- Workstations and unused mobile devices are locked automatically.
- Laptops, smartphones and tablets are never left unattended.
- Disable the “Autorun” function of external media.
- Store or copy all data on a server or NAS (Network Area Storage).
ADVANCED PROTECTION
- Discarded hard drives, media and printers containing data are physically destroyed.
- Prohibit connection of personal devices to the organization’s information system.
- Encrypt hard drives on laptops.
- Sensitive or confidential data is transmitted only in encrypted form.
- Technically prevent the connection of unregistered portable media.
- Data stored in the cloud is encrypted (eg BoxCryptor).
- The guarantees offered by the cloud provider correspond to the criticality level of the stored information.
- External media players such as USB sticks are checked for viruses before they are connected to a computer.
SECURING SERVERS AND NETWORK COMPONENTS
The security measures to be taken to secure a server depend on the services that it runs, the level of confidentiality of the data it contains, and the risks involved.
System administrators or network administrators are responsible for the preparation, installation, and maintenance of the servers. The role of a system administrator does not stop with the installation and configuration of machines. This person also holds a key role in network security over the long term.
The more connected a company is, the more vulnerable it is. New communication or sharing technologies (e-mail, mobility, video conferencing, online tools) have become part of our daily lives. These technologies also generate new challenges for the security of your business.
BASIC PROTECTION
- Change all default passwords and disable unused accounts.
- Protect Wi-Fi with WPA2 encryption.
- Close unused ports and services.
- Avoid remote connection to servers.
- Use secure applications and protocols.
- Security logs on servers and firewalls are kept for a period of at least 1 month.
- The public Wi-Fi network is separate from the corporate network.
ADVANCED PROTECTION
- Security logs are kept for a period of at least 6 months Protect enterprise Wi-Fi by WPA2.
- Enterprise with a system
device registration. - Reinforce all systems according to the supplier’s recommendations.
- Use a network (logically) separate from the user’s network for server administration.
- Evaluate all events and alerts for servers, firewalls and network components.
- An alert-based analysis and alerting system for detecting malicious behavior (SIEM).
- An IDS / IPS system (Intrusion Detection / Prevention System) monitors all communications.
- Physical access to servers and network components is limited to a minimum number of people.
- All physical access to servers and network components is logged.
- Perform intrusion tests and vulnerability scans.
SECURE REMOTE ACCESS
Mobile staff, adoption of cloud applications, and expanded network access for consultants and business partners are blurring the boundaries of the traditional network security perimeter. Organizations must deploy remote access security solutions in order to keep data secure when employees are inside and outside of the office.
When enterprise resources are dispersed across local, cloud, and virtual applications, it is critical to have a central management point from which uniform access controls will be defined and enforced to ensure security and optimal transparency.
BASIC PROTECTION
- Remote access should be closed automatically when idle for a period of time.
- Limit remote access to what is strictly necessary.
- All connections to the corporate network are secure and encrypted.
ADVANCED PROTECTION
- Only allow Virtual Private Network (VPN) connections from endpoints.
- Strong authentication is used when connecting from outside public networks.
- Remote access is limited to the IP addresses of the providers and the necessary regions.
HAVE A PLAN FOR CONTINUITY OF ACTIVITIES AND AN INCIDENT MANAGEMENT PLAN
This is the set of measures aimed at ensuring, under various crisis scenarios (including in the face of extreme shocks), the maintenance of services essential to the business. A Business Continuity Plan (BCP) includes risk analysis to deal with multiple scenarios. It can be an IT problem, a data breach attack, a natural disaster on a site, a fire, or another scenario.
The business continuity plan provides for the maintenance of the company’s essential services such as the work of certain services on a fallback site. It also provides for the planned recovery of activities.
A Business Continuity Plan (BCP) is essential for any sector when there is a risk of disruption of critical activities that may lead to economic losses or to reputation losses of the company.
Responding correctly to scenarios, including sending a clear and precise alert using a crisis management system, can increase credibility among employees and customers.
The management and control of risks associated with a change is essential to ensure the sustainability of a company.
It is necessary to carry out one or more crisis risk analyzes:
Analysis of the repercussions on the operations: in the context of a crisis scenario, what are the activities, the processes essential to the durability of the company?
IT risk analysis: Is the use of IT essential to the smooth running of the business? In case of affirmation, what impacts should we expect to face?
Chemical, Flood or Fire Risk Analysis: Does the company have a hazardous substance that can ignite? Is it located in a flood risk zone? Is it surrounded by other companies equipped with dangerous substances? A disaster can be caused by the proximity of other risks of internal or external origin.
BASIC PROTECTION
- Have an incident management plan to respond to an incident
- Have a business continuity plan to preserve the business
- All workers must know the point of contact to report an incident
- Distribute and update contact point information (internal and external contacts, management and technical contacts, etc.)
- Report all incidents to the management
ADVANCED PROTECTION
- Evaluate and test these plans annually.
- Evaluate the advisability of insurance against incidents of
cybersecurity. - Install emergency devices for utility services (electricity, telephone, Internet, etc.).
CONCLUSION
Cybercrime is growing at a fast pace and more and more businesses are being targeted. In the United States, nearly 44% of small businesses have been victims of a cyberattack and the number continues to increase each year. This crime could cost more than $ 2 billion in 2019. This is four times more than in 2015.
Developing a strong, multi-layered security strategy using each of the 12 types of cybersecurity that we outlined can save a business.
Continuous training of employees and the implementation of security technologies will provide the first line of defense and significantly reduce the number of security breaches.
Finally, a reliable backup and recovery solution will be the second and most important layer that gives businesses the ability to reboot quickly in the event of a major incident.
THIS TYPES OF CYBERSECURITY GUIDE HAS BEEN DEVELOPED BY TECHNICAL EXPERT HICHAM, IN PARTNERSHIP WITH “cyberexperts.com“. IT IS BASED ON CONTRIBUTIONS AND BEST PRACTICES IN ORDER TO HAVE A ROBUST DEFENSE AND FACE THE DIGITAL THREAT.
Note: The information provided on this types of cybersecurity guide is exclusive of a general nature and do not intend to take into consideration any particular situation.